BY ORDER OF THE AIR FORCE PAMPHLET 91-215 SECRETARY ...
BY ORDER OF THE AIR FORCE PAMPHLET 91-215 SECRETARY ...
BY ORDER OF THE AIR FORCE PAMPHLET 91-215 SECRETARY ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
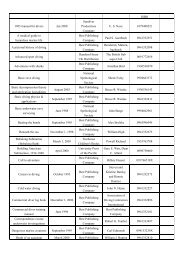
Figure A2.26. Example Mission Protection Application.<br />
Situation: A major material management center uses a computer to help management<br />
the complex distribution and cost accounting needed to successfully carry out the mission.<br />
If this computer were to be seriously impaired in any way, the mission could be down for<br />
a time ranging from several hours to several days. The decision is made to complete an<br />
in-depth mission protection analysis of the computer operation. The individual responsible<br />
for the applications uses his hazard ID toolbox to select the following tool for this<br />
important mission protection analysis.<br />
TOOLS TO BE USED<br />
Operations analysis (to establish the full dimension of the operation)<br />
What if analysis (to establish contingency-type threats to the mission)<br />
Interview tool (to get inputs from personnel involved in the operation)<br />
Several Logic Diagrams (used to explore several of the higher risk issues revealed<br />
by the tools above.)<br />
Interface tool (used to detect any threats from non-related functions)<br />
Change analysis tool (to assess any intentional or unintentional change in the last<br />
1or2 years.<br />
The products derived from this analysis is essentially the same as the hazard<br />
identification assessments except that the focus is on those things, whether they cause<br />
physical damage or injury or not, that impact the mission of the system.<br />
66