ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
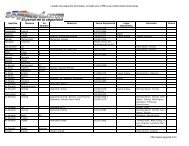
Active Directory Checklist, V1R1.2 Field Security Operations<br />
22 September 2006 Defense Information Systems Agency<br />
DS10.0250 Privileged Group Membership - Inter-Forest<br />
STIG ID \ V-Key DS10.0250 \ V0008549<br />
Severity Cat II<br />
Short Name Privileged Group Membership - Inter-Forest<br />
IA Controls ECLP-1, ECPA-1<br />
MAC /Conf 1-CSP, 2-CSP, 3-CSP<br />
References AD STIG 2.3.3.6<br />
Long Name: Accounts from another AD forest are members of Windows built-in<br />
administrative groups and the other forest is not under the control of the same<br />
organization or subject to the same security policies.<br />
Checks:<br />
• Start the Active Directory Users and Computers console (“Start”, “Run…”,<br />
“dsa.msc”).<br />
• Select and expand the left pane item that matches the name of the domain being<br />
reviewed.<br />
• Select the Users container<br />
- For each of the Domain Admins, Enterprise Admins, Schema Admins, and<br />
Group Policy Creator Owners groups:<br />
-- Double-click on the group and select the Members tab<br />
-- Examine the defined accounts to see if they are from a domain that is not in the<br />
forest being reviewed.<br />
• Select the Builtin container<br />
- If the Incoming Forest Trust Builders group is defined:<br />
-- Double-click on the group and select the Members tab<br />
-- Examine the defined accounts to see if they are from a domain that is not in the<br />
forest being reviewed.<br />
• If any account in an administrative group is from a domain outside the forest<br />
being reviewed and that outside forest is not maintained by the same organization<br />
(e.g., enclave) or subject to the same security policies, then this is a Finding.<br />
Note: An account that is from an outside domain appears in the format “outsidedomain-NetBIOSname\account”<br />
or “account@outside-domain-fully-qualifiedname”.<br />
Examples are “AOFN21\jsmith” or “jsmith@AOFN21.DISA.MIL”. It may<br />
be necessary to use the AD Domains and Trusts (domain.msc) console to determine<br />
if the domain is from another AD forest.<br />
Note: It is possible to move the highly privileged AD security groups out of the AD<br />
Users container. If the Domain Admins, Enterprise Admins, Schema Admins, or<br />
Group Policy Creator Owners groups are not in the AD User container, ask the SA<br />
for the new location and use that location for this check.<br />
UNCLASSIFIED<br />
5-23