ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
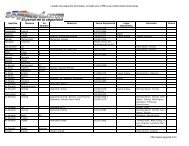
Active Directory Checklist, V1R1.2 Field Security Operations<br />
22 September 2006 Defense Information Systems Agency<br />
2.4.8 Domain Controller Characteristics<br />
The checks in this section address some miscellaneous characteristics that affect the operational<br />
integrity of each domain controller.<br />
DS10.0140 Domain Controller Dedication<br />
STIG ID \ V-Key DS10.0140 \ V0008326<br />
Severity Cat III<br />
Short Name Domain Controller Dedication<br />
IA Controls DCSP-1<br />
MAC /Conf 1-CSP, 2-CSP<br />
References AD STIG 2.3.1.5<br />
Long Name: The domain controller is not dedicated to that function. It is hosting an application<br />
such as a database server, e-mail server, e-mail client, web server, or DHCP<br />
server.<br />
Checks:<br />
• Start the Services console (“Start”, “Run…”, “services.msc”).<br />
• Check to see if any application-related services have the “Started” status.<br />
*Examples* of some services that indicate the presence of applications are:<br />
- DHCP Server for DHCP server<br />
- IIS Admin Service for IIS web server<br />
- Microsoft Exchange System Attendant for Exchange<br />
- MSSQLServer for SQL Server<br />
- ADAM_[instance] for ADAM directory service.<br />
• If any application-related services have the “Started” status, then this is a Finding.<br />
Note: The Microsoft Windows-based Domain Name System (DNS) server *is* an<br />
acceptable application because, when securely deployed, it is integrated into AD.<br />
UNCLASSIFIED<br />
5-8