ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Active Directory Checklist, V1R1.2 Field Security Operations<br />
22 September 2006 Defense Information Systems Agency<br />
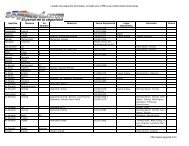
5. MANUAL CHECK PROCEDURES<br />
This section of the Checklist describes the procedures to be used to conduct a manual review for<br />
the Active Directory STIG requirements. The results from the procedures in this section can be<br />
recorded on a copy of the Review Results Report in Section 2.<br />
5.1 Review Process Information<br />
All of the AD domain and forest checks in this document are performed on a Windows domain<br />
controller using a Windows account that is a member of the Domain Admins security<br />
group. While it is possible to perform these checks remotely, the documented procedures<br />
assume that the reviewer is using the console of the domain controller.<br />
The checks for synchronization and maintenance products require the input and assistance of the<br />
administrator of the application. A Windows account with administrative privileges for the<br />
application is required.<br />
It is assumed that the reviewer is familiar with the tools and procedures documented in the<br />
Windows Security Checklists. While the procedures in this document are generally explicit,<br />
basic procedures such as the process for checking file system ACLs are not documented.<br />
The following tools are used during the review process and are available on all Windows domain<br />
controllers:<br />
- Windows Explorer<br />
- Microsoft Management Console (MMC) Snap-ins:<br />
- AD Users and Computers (dsa.msc)<br />
- AD Domains and Trusts (domain.msc)<br />
- AD Sites and Services (dssite.msc)<br />
- Services (services.msc)<br />
- Registry Editor<br />
- Command Prompt Invocation:<br />
- Shared resources (net share)<br />
- Directory Service Query (dsquery.exe) - Win2K3<br />
The following tool is used during the review process and is only available if the Windows<br />
Support Tools have been installed:<br />
- Command Prompt Invocation:<br />
- Support Tools Domain Manager (netdom.exe)<br />
The following information should be available to accelerate the review process:<br />
- AD trust relationship documentation<br />
[Appendix B provides examples.]<br />
- Lists of accounts assigned to AD privileged groups (Domain Admins, Enterprise Admins,<br />
Schema Admins, Group Policy Creator Owners, and Incoming Forest Trust Builders)<br />
- List of accounts with the right to create AD objects (e.g., accounts, printers), but that are<br />
not members of the built-in AD privileged groups<br />
UNCLASSIFIED<br />
5-1