ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
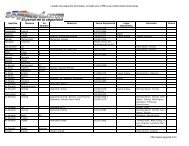
Active Directory Checklist, V1R1.2 Field Security Operations<br />
22 September 2006 Defense Information Systems Agency<br />
DS05.0450 Synch\Maint Disaster Recovery Documentation<br />
STIG ID \ V-Key DS05.0450 \ V0011780<br />
Severity Cat III<br />
Short Name Synch\Maint Disaster Recovery Documentation<br />
IA Controls COEF-2<br />
MAC /Conf 1-CSP, 2-CSP<br />
References AD STIG 2.3.6<br />
Long Name: Disaster recovery plans do not include identification of products used in routine,<br />
scheduled synch\maint operations.<br />
Checks:<br />
• Interview the Application SA.<br />
• Obtain a copy of the site’s disaster recovery planning documents.<br />
• Verify that the disaster recovery plans include documentation of the products used<br />
in routine, scheduled synch\maint operations.<br />
• If the disaster recovery plans do not include documentation of the products, then<br />
this is a Finding.<br />
DS05.0460 Synch\Maint Security Patch Implementation<br />
STIG ID \ V-Key DS05.0460 \ V0011781<br />
Severity Cat II<br />
Short Name Synch\Maint Security Patch Implementation<br />
IA Controls VIVM-1<br />
MAC /Conf 1-CSP, 2-CSP, 3-CSP<br />
References AD STIG 2.3.7<br />
Long Name: Security related patches for synch\maint products are not applied or the<br />
application status is not documented.<br />
Checks:<br />
• Interview the Application SA.<br />
• Obtain a copy of the site’s policy that addresses security patch implementation.<br />
• Verify that the local policy requires all vendor-provided security patches to be<br />
applied and the status to be documented for synch\maint products.<br />
• If there is no policy that requires all the vendor-provided security patches to be<br />
applied and the status to be documented, then this is a Finding.<br />
3.6 Active Directory Application Mode Instance<br />
This section is reserved for future interview checks for ADAM instances.<br />
UNCLASSIFIED<br />
3-31