ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
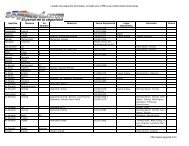
Active Directory Checklist, V1R1.2 Field Security Operations<br />
22 September 2006 Defense Information Systems Agency<br />
DS05.0410 Synch\Maint Remote Access Encryption<br />
STIG ID \ V-Key DS05.0410 \ V0011777<br />
Severity Cat II<br />
Short Name Synch\Maint Remote Access Encryption<br />
IA Controls EBRU-1<br />
MAC /Conf 1-CS, 2-CS, 3-CS<br />
References AD STIG 2.3.4<br />
Long Name: Remote access to a synch\maint implementation is not encrypted.<br />
Checks:<br />
• Interview the Application SA.<br />
• If the information obtained in checks DS05.0380 and DS05.0400 indicate the<br />
synch\maint implementation does *not* support and utilize privileged or<br />
non-privileged remote access, then this check is Not Applicable.<br />
• If the synch\maint implementation *does* support and utilize remote access,<br />
review the application documentation and site network diagram(s) to determine if<br />
FIPS 140-2-validated encryption is used to protect the network traffic.<br />
- This includes encryption of the data on the host before transmission, the use of<br />
LDAPS or HTTPS protocol, or the use of network components (such as a VPN)<br />
to perform encryption.<br />
• If the synch\maint implementation supports and utilizes remote access and FIPS<br />
140-2-validated encryption is not used, then this is a Finding.<br />
Note: The use of properly configured (as validated through the Windows Checklist)<br />
Windows Terminal Services meets this requirement.<br />
UNCLASSIFIED<br />
3-29