ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
ACTIVE DIRECTORY SECURITY CHECKLIST ... - Leet Upload
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
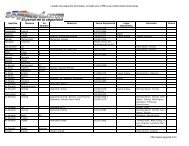
Active Directory Checklist, V1R1.2 Field Security Operations<br />
22 September 2006 Defense Information Systems Agency<br />
DS05.0350 Synch\Maint Certificate Validity Checking<br />
STIG ID \ V-Key DS05.0350 \ V0011772<br />
Severity Cat III<br />
Short Name Synch\Maint Certificate Validity Checking<br />
IA Controls IAAC-1<br />
MAC /Conf 1-CS, 2-CS, 3-CS<br />
References AD STIG 2.3.3.8<br />
Long Name: A synch\maint product that utilizes PKI certificates does not perform certificate<br />
validation that includes CRL or OCSP checking.<br />
Checks:<br />
• Interview the Application SA.<br />
• Review the application documentation or configuration settings to determine if<br />
the synch\maint implementation utilizes PKI certificates.<br />
• If PKI certificates are *not* used, then this check is Not Applicable.<br />
• If PKI certificates *are* used, review the application documentation or<br />
configuration settings to determine if the product performs certificate validation<br />
that includes CRL or OCSP checking.<br />
- Note that certificates could be used in multiple parts of the implementation such<br />
as client authentication of the server *and* server authentication of the client. All<br />
uses should be examined.<br />
• If the synch\maint implementation utilizes PKI certificates and the product does<br />
not perform certificate validation that includes CRL or OCSP checking, then this<br />
is a Finding.<br />
Note: At this time it is understood that SimpleSync, MIIS, and IIFP do *not*<br />
perform CRL or OCSP checking.<br />
UNCLASSIFIED<br />
3-24