Computer Security Threat Monitoring and Surveillance
Computer Security Threat Monitoring and Surveillance
Computer Security Threat Monitoring and Surveillance
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
6.5 Tasks<br />
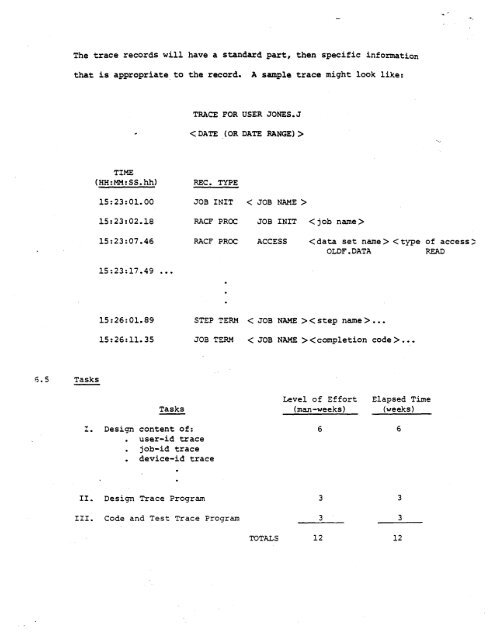
The trace records will have a st<strong>and</strong>ard part, then specific information<br />
that is appropriate to the record. A sample trace might look like:<br />
TIME<br />
(HH:MM:SS. hh) REC. TYPE<br />
15:23:01.00 JOB INIT<br />
15:23:02.18 RACF PROC<br />
15:23:07.46 RACF PROC<br />
15:23:17.49 •••<br />
15:26:01.89 STEP TERM<br />
15:26:11.35 JOB TERM<br />
Tasks<br />
!. Design content of:<br />
user-id trace<br />
job-id trace<br />
device-id trace<br />
II. Design Trace Program<br />
III. Code <strong>and</strong> Test Trace Program<br />
TRACE FOR USER JONES.J<br />
<br />
< JOB NAME ><br />
JOB INIT < job name><br />
ACCESS < step name > •••<br />
< JOB NAME > •••<br />
TOTALS<br />
Level of Effort<br />
(man -weeks)<br />
6<br />
3<br />
3<br />
12<br />
Elapsed Time<br />
(weeks)<br />
6<br />
3<br />
3<br />
12