DIGIPASS Authentication for FortiGate VPN SSL IDENTIKEY - Vasco
DIGIPASS Authentication for FortiGate VPN SSL IDENTIKEY - Vasco
DIGIPASS Authentication for FortiGate VPN SSL IDENTIKEY - Vasco
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
1 Reader<br />
<strong>DIGIPASS</strong> <strong>Authentication</strong> <strong>for</strong> Fortigate <strong>SSL</strong>-<strong>VPN</strong><br />
This Document is a guideline <strong>for</strong> configuring the partner product with <strong>IDENTIKEY</strong> SERVER or<br />
Axsguard IDENTIFIER. For details about the setup and configuration of IDENTIEKEY SERVER and<br />
Axsguard IDENTIFIER, we refer to the Installation and administration manuals of these products.<br />
Axsguard IDENTIFIER is the appliance based solution, running <strong>IDENTIKEY</strong> SERVER by default.<br />
Within this document, VASCO Data Security, provides the reader guidelines <strong>for</strong> configuring the<br />
partner product with this specific configuration in combination with VASCO Server and Digipass.<br />
Any change in the concept might require a change in the configuration of the VASCO Server<br />
products.<br />
The product name`<strong>IDENTIKEY</strong> SERVER`will be used throughout the document keeping in mind<br />
that this document applies as well to the Axsguard IDENTIFIER.<br />
2 Overview<br />
The purpose of this document is to demonstrate how to configure <strong>IDENTIKEY</strong> SERVER to work<br />
with a Fortigate device. <strong>Authentication</strong> is arranged on one central place where it can be used in a<br />
regular <strong>VPN</strong> or <strong>SSL</strong>/<strong>VPN</strong> connection.<br />
3 Problem Description<br />
The basic working of the Fortigate is based on authentication to an existing media (LDAP,<br />
RADIUS, local authentication …). To use the <strong>IDENTIKEY</strong> SERVER with Fortigate, the external<br />
authentication settings need to be changed or added manually.<br />
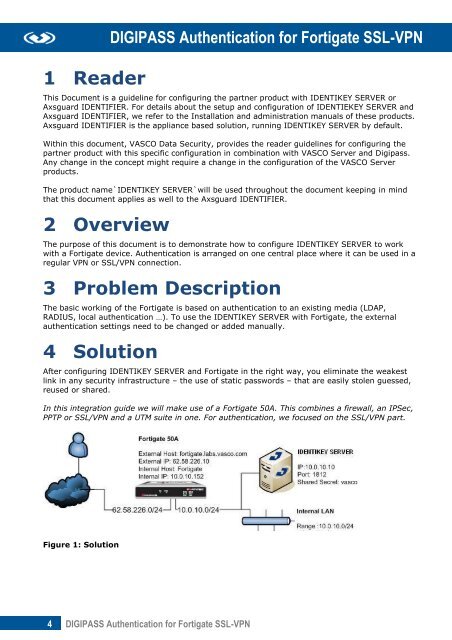
4 Solution<br />
After configuring <strong>IDENTIKEY</strong> SERVER and Fortigate in the right way, you eliminate the weakest<br />
link in any security infrastructure – the use of static passwords – that are easily stolen guessed,<br />
reused or shared.<br />
In this integration guide we will make use of a Fortigate 50A. This combines a firewall, an IPSec,<br />
PPTP or <strong>SSL</strong>/<strong>VPN</strong> and a UTM suite in one. For authentication, we focused on the <strong>SSL</strong>/<strong>VPN</strong> part.<br />
Figure 1: Solution<br />
4 <strong>DIGIPASS</strong> <strong>Authentication</strong> <strong>for</strong> Fortigate <strong>SSL</strong>-<strong>VPN</strong>







![KB [100006] - Vasco](https://img.yumpu.com/12539350/1/184x260/kb-100006-vasco.jpg?quality=85)