Galaxy Music strip ad 21cmx3cm.pdf 1 Feb/13/13 5:27 PM
Galaxy Music strip ad 21cmx3cm.pdf 1 Feb/13/13 5:27 PM
Galaxy Music strip ad 21cmx3cm.pdf 1 Feb/13/13 5:27 PM
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Galaxy</strong> <strong>Music</strong> <strong>strip</strong> <strong>ad</strong> <strong>21cmx3cm</strong>.<strong>pdf</strong> 1 <strong>Feb</strong>/<strong>13</strong>/<strong>13</strong> 5:<strong>27</strong> <strong>PM</strong>
1<br />
UGANDA/INTERNATIONAL - pctechmag.com<br />
KENYA EDITION - ke.pctechmag.com<br />
GHANA EDITION - gh.pctechmag.com<br />
3 NIGERIA EDITION - ng.pctechmag.com<br />
3<br />
<br />
<br />
2
EDITORIAL<br />
2<br />
SOCIAL INNOVATION? iHub Nairobi, just like many other hubs is not just about work. They also act as focal point for the tech community to<br />
come together, learn and, of course party. SEE FULL IN THIS MONTH’S COVER STORY<br />
4 | Editorial team, and Editor’s Notes<br />
6 | Verbatim<br />
THE WALL 6<br />
7 | Numbers: The Mobile World Congress 20<strong>13</strong><br />
(Infographic)<br />
UPDATE 8<br />
8 | Uganda to introduce law to regulate mobile services<br />
8 | 50% Bonus on Data from Airtel Uganda<br />
9 | MTN introduces Nokia Lumia<br />
9 | Google Glass one step close<br />
10 | Adobe Creative Suit goes free (sort of)<br />
11 | MTN’s cross-border fibre cable commissioned<br />
12 | Kenya: SIM Registration Laws Come Into Effect<br />
12 | MTN, RIM partner on Blackberry 10<br />
<strong>13</strong> | Kenya Begins Construction Of ‘Silicon’ City Konza<br />
Artistic Impression of what is intended to be Africa’s “Silicon Valley”.<br />
WHAT’S NEW 14<br />
14 | BlackBerry’s Z10 Smartphone<br />
14 |Panasonic 4K 20-inch tablet<br />
15 | Google’s Chrome Pixel<br />
15 | New Samsung Refrigerator<br />
COVER STORY 16<br />
17 | Inside East Africa’s largest Innovation Hubs<br />
“Hubs” are all over the place these days. And if you look<br />
closely, it means there’s one universal problem: how to<br />
turn techies into entreprenuers. So this article, part of<br />
which is from a report from a research that used iHub<br />
(Nairobi) as a case study, seeks to tell us how the business<br />
of coding is turning into real business!<br />
FEATURES 24<br />
25 | 10 things the comments section taught me about the<br />
Web<br />
<strong>27</strong> | Market Analysis: Mobile Payments In Emerging Nations<br />
28 | The Dark Side of Computers<br />
FEATURES/BLOGS 32<br />
32 | Ecommerce Is Now A Trillion Dollar Industry: Here’s<br />
How It Happened<br />
33 | Lock up your mailbox<br />
34 | Why life through Google Glass...<br />
REVIEWS 36<br />
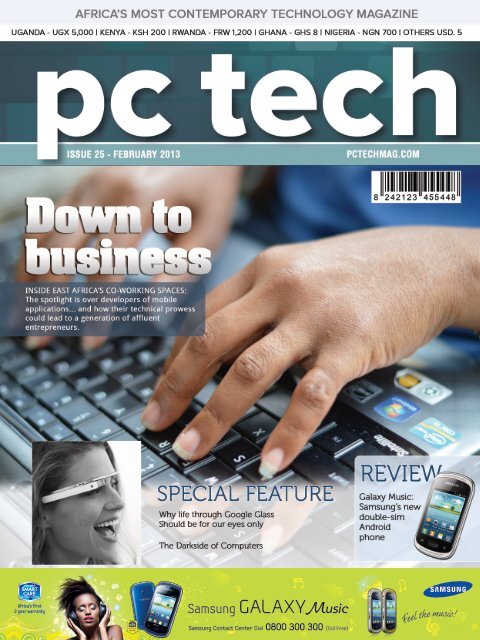
36 | Samsung <strong>Galaxy</strong> <strong>Music</strong><br />
38 | Nokia Lumia 920<br />
40 | Orange Money<br />
41 | TOSHIBA Satellite P845t-101<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
3
EDITORIAL<br />
4<br />
CHIEF EDITOR/CEO<br />
ALBERT MUCUNGUZI<br />
albert@pctechgrop.net<br />
+256 792 619812 / 782 619812<br />
DIRECTOR, West Africa<br />
RICHARD BOATENG, PhD<br />
richard@pearlrichards.org<br />
FINANCE MANAGER<br />
WYCLEF RUSHAJU<br />
wyclef@pctechgroup.net<br />
+256 703 473073<br />
EDITOR<br />
JEDDY GENRWOT<br />
jeddy@pctechmagazine.com<br />
WEBSITE ADMINISTRATORS<br />
EPHRAIM BATAMBUZE<br />
ebatambuze@gmail.com<br />
NORMAN MUHWEZI<br />
norman@pctcehmagazine.com<br />
BLOGGERS<br />
SIMON KAHERU<br />
skaheru@smsmedia.info<br />
DOUGLAS B. KASYABA<br />
kasyaba587@gmail.com<br />
PATRICK TUMUSIIME<br />
marpat2000@gmail.com<br />
NIGERIA<br />
Ishola Abdulkabeer<br />
abdulkabeerishola@gmail.com<br />
ADVERTISING ENQUIRIES<br />
<strong>ad</strong>vertising@pctechmagazine.com<br />
+256 792 619812<br />
PUBLISHER<br />
PC Tech Communications Ltd<br />
Plot 14 Martyrs’ Lane, Ntinda (Minister’s Village)<br />
P. O. Box 32180, Kampala, Uganda<br />
www.pctechmag.com<br />
© COPYRIGHT 20<strong>13</strong><br />
PC Tech Magazine is published 11 times a year<br />
by PC Tech Communications Ltd. The name PC<br />
Tech Magazine is a registered tr<strong>ad</strong>emark and is<br />
property of PC Tech Communications Ltd.<br />
Welcome to yet another issue of Your Most Contemporary Technology<br />
Magazine.<br />
It is, of course, my pleasure to introduce our<br />
new editor, Jeddy Genrwot, a young and dynamic<br />
guy that’s worked so hard to see this issue<br />
through.<br />
In the coming months, you’ll be seeing more of<br />
his name through the pages.<br />
In the news this month, mTN commissioned<br />
the cross-border fibre cable at Katuna, Uganda/<br />
Rwanda border, a landmark event that effectively<br />
means Uganda has access to an alternative<br />
internet “route” in the event the default one goes<br />
down.<br />
The same company then introduced Nokia’s flagship Windows 8 Phone,<br />
the Nokia lumia. I got the sense that microsoft may be borrowing a bullet<br />
from Google’s gun and coming down to this (Sub Saharan market) that has<br />
long been dominated by chinese manufacturers.<br />
In the cover story, we look at three Innovation Hubs across east Africa.<br />
These are co-working spaces that primarily target tech-minded young people,<br />
and attempt to help them become better entrepreneurs and - in some cases -<br />
help them get access to investors.<br />
We speak to Richard Zulu from Uganda’s outbox Hub, and also feature<br />
excerpts from a research report conducted in Kenya with iHub as a case<br />
study.<br />
Don’t miss the reviews, and Special Features, including one on “The<br />
Darkside of computers”.<br />
Until next month!<br />
Albert mucunguzi<br />
Subscribe<br />
and save!<br />
6 issues at the price of 5<br />
11 Issues at the price of 10<br />
2 FREE COPIES<br />
Fill in the form and bring / send it to:<br />
PC Tech Communications, Plot 14, Martyrs’ Lane, Ntinda P. O. Box 32180, Kampala, Uganda<br />
I would like to subscribe to PC Tech Magazine for: 6 issues 11 issues<br />
tick your choice<br />
I have enclosed UGX 25,000 (USD 10) UGX 50,000 (USD 25) as payment for my subscription.<br />
( Cash Cheque) tick where appropriate<br />
NAME: _________________________________________________________________<br />
ADDRESS: ______________________________________________________________<br />
TEL: ___________________________________________________________________<br />
EMAIL: _________________________________________________________________<br />
DELIVERY ADDRESS: _______________________________________________________<br />
________________________________________________________________________<br />
________________________________________________________________________<br />
________________________________________________________________________<br />
Please double check your <strong>ad</strong>dress and ensure that it is accurate as PC Tech shall not be held responsible for non delivery due to wrong /<br />
incomplete / inaccurate <strong>ad</strong>dresses.<br />
www.pctechmagazine.com/subscribe<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
+256 792 619 812 / +256 703 473 073<br />
EDITORIAL
THE WALL<br />
6<br />
Think of this as your<br />
Facebook Wall, now called<br />
Timeline. Here, we publish<br />
anything. Yes, ANYTHING.<br />
So what’s there this month<br />
may not necessarily be<br />
there next.<br />
‘<br />
Verbatim<br />
“We want Google to be the third half of your brain.”<br />
“There are a lot of amazing things that Steve’s le<strong>ad</strong>ership achieved —<br />
Windows 8, the Surface computer, Bing, Xbox. Is it enough? No. He<br />
and I are not satisfied that in terms of breakthrough things we are doing<br />
everything possible.”<br />
Former Chief Executive and current chairman of Microsoft BILL gATES comments during a recent interview on NBSC<br />
Sergey Brin Russian-born American computer scientist and entrepreneur is also along side Larry Page, a co founder<br />
of Google<br />
“I don’t care if you’re a billionaire. If you haven’t started a company,<br />
really gambled your resume and your money and maybe even your<br />
marriage to just go crazy and try something on your own, you’re no<br />
pirate and you aren’t in the club”<br />
Michael Arrington, TechCrunch<br />
One of the huge mistakes people make is that they try to force an<br />
interest on themselves. You don’t choose your passions; your passions<br />
choose you.<br />
After learning that Microsoft CEO Steve Ballmer would not be giving the keynote speech at CES in 20<strong>13</strong>, and inste<strong>ad</strong><br />
Co-founder and CEO of Amazon.com, Inc JEFF BEzOS<br />
“Every young person one day will be entitled automatically to change<br />
his or her name on reaching <strong>ad</strong>ulthood in order to disown youthful<br />
hijinks stored on their friends’ social media sites.”<br />
STEVE BALLMER, Microsoft CEO To the Wall Street Journal<br />
“We didn’t miss cellphones, but the way that we went about it didn’t<br />
allow us to get the le<strong>ad</strong>ership. It’s clearly a mistake,”<br />
Former Chief Executive and current chairman of Microsoft BILL gATES comments during a recent interview on NBSC<br />
Thick skin will be a necessity for technology companies in the coming<br />
years of the digital age, because they will find themselves beset by<br />
public concerns over privacy, security and user protections…They’ll<br />
also have to hire more lawyers. Litigation will always outpace genuine<br />
legal reform, as any of the technology giants fighting perpetual legal<br />
battles over intellectual property, patents, privacy and other issues<br />
would attest”<br />
STEVE BALLMER, Microsoft CEO<br />
INFOGRAPHIC: The Mobile World Congress 20<strong>13</strong><br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
Turn to page 23<br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
THE WALL
UPDATE<br />
TOP STORIES THIS MONTH<br />
8<br />
Uganda to introduce new law<br />
to regulate Mobile Services<br />
UCC boss praises Orange Uganda<br />
Uganda’s telecommunications regulator announced<br />
that it will introduce a new law that will see more<br />
regulation of <strong>ad</strong>vertising on short text messaging<br />
services and mobile money business in the East African<br />
country.<br />
The Uganda Communications Commission (UCC)<br />
said that the new law will “restore sanity” and help<br />
“improve the quality of services that mobile telephone<br />
companies have <strong>ad</strong>ded to their platforms.”<br />
The statement from the UCC continued to say that<br />
the new law will help these services from continuing to<br />
be “a safe haven for fraud to fleece the unsuspecting<br />
public.”<br />
According to the UCC Executive Director Godfrey<br />
Mutabazi “the most common problems have been the<br />
loss of mobile money, dropped telephone calls, free<br />
airtime promotions, SMS promotions where the public<br />
is asked to vote through certain codes, unsolicited<br />
messaging services where the public loses money by<br />
replying by text message to certain numbers, as well as<br />
unexplained airtime deductions.”<br />
Mutabazi singled out Orange Telecom as the “only<br />
mobile operator which has tried to stick to prudent<br />
business by protecting its customers.”<br />
He <strong>ad</strong>ded that the “UCC and the Bank of Uganda<br />
are in <strong>ad</strong>vanced stages of coming up with a law on<br />
mobile commerce as well as make amendments to the<br />
1997 Uganda Mobile Communications Act because<br />
it has been found to be lacking in the prosecution of<br />
fraudsters.”<br />
“Although the prices of Internet service have<br />
considerably dropped in the last two years, the quality<br />
has been compromised by unprofessional activities by<br />
the telephone operators,” he continued.<br />
50% Bonus on Data from Airtel Uganda<br />
AIRTEL UGANDA launched 50% bonus data campaign<br />
that which is a way of giving back to our data<br />
customers. This will mean that for every purchase of<br />
a data bundle, one will get a bonus of 50% on that<br />
purchase.<br />
Our aim is to be the most loved brand in the daily<br />
lives of Ugandans and we recognize the importance of<br />
internet in the transformation of Uganda as a country<br />
and in the lives of Ugandans as a people. We are<br />
continuously trying to make our services more relevant<br />
to our customers.<br />
Mr. V.G Somasekhar, the Managing Director, Airtel<br />
Uganda has this to say, “With the 50% bonus our<br />
customers will be able to enjoy a wholesome internet<br />
experience with a reliable and abundant service. We<br />
hope with this offer to get more people to access our<br />
affordable data package and transform their lives by<br />
keeping up with the times.”<br />
Airtel launched 3.75G in august 2012 and so far<br />
has the largest 3G Network and the most affordable<br />
packages.<br />
On 5th <strong>Feb</strong>ruary Airtel also launched a new<br />
partnership with UGO to avail all her customers with<br />
free local content through www.ugo.co.ug<br />
IN BRIEF<br />
Google Glass<br />
one step closer<br />
GOOGLE HAS INVITED software<br />
developers to get their hands on its<br />
Project Glass prototypes, in the hope<br />
that they will start work on new and<br />
innovative apps that take <strong>ad</strong>vantage<br />
of the upcoming augmented reality<br />
he<strong>ad</strong>set.<br />
Based around the same technology<br />
as its Android smartphones and tablets,<br />
Google Glass was first unveiled in<br />
April last year as a prototype wearable<br />
computing device that projects a small,<br />
discrete image into one eye of the<br />
wearer.<br />
Original estimates suggested the<br />
device would cost the same as a mid- to<br />
high-end smartphone – in other words,<br />
roughly $250 to $600. However, that<br />
target was far below what early <strong>ad</strong>opters<br />
are being charged for the privilege,<br />
which is $1,500, something that will<br />
hopefully change when the technology<br />
reaches mainstream consumers.<br />
Project Glass isn’t without its<br />
competitors: sunglasses specialist<br />
Oakley is working on a version of its<br />
own, while Vuzix alre<strong>ad</strong>y sells a range<br />
of Glass-like devices. Even Motorola<br />
is getting in on the act, albeit with a<br />
ruggedised version aimed more at the<br />
military than the consumer. That’s why<br />
Google is hoping it will have generated<br />
developer interest in its Glass Foundry<br />
days in San Francisco and New York,<br />
to create unique new apps specifically<br />
for Project Glass. The invite-only events<br />
will see developers given access to<br />
the hardware and underlying software<br />
interfaces, in order to begin work on<br />
applications that can make the most of<br />
the wearable computer system.<br />
The San Francisco event took place<br />
at the end of January, and the New<br />
York event was held at the beginning of<br />
<strong>Feb</strong>ruary.<br />
MTN introduces<br />
Nokia Lumia<br />
MTN UGANDA ANNOUNCED THE availability<br />
of the Nokia Lumia 920 and Lumia 820<br />
smartphones, <strong>ad</strong>ding its name to the growing<br />
list of operators globally selling these flagship<br />
Windows 8 Phone devices.<br />
“We’re excited to work with Nokia to bring<br />
one of the most innovative smartphone on the<br />
market, – the Nokia Lumia 920. With unrivalled<br />
innovations in imaging technology, wireless<br />
charging and a bright, sensitive display, we<br />
think the Lumia 920 is going to turn a lot of<br />
he<strong>ad</strong>s.” said Ernst Fonternel, MTN Uganda Chief<br />
Marketing Officer”<br />
“We welcome MTN Uganda’s decision to<br />
offer the Nokia Lumia 920 and Lumia 820 to our<br />
valued consumers in Uganda. With a growing<br />
demand for smartphones across East Africa,<br />
we believe this announcement continues the<br />
momentum behind our Lumia range of devices<br />
and the bro<strong>ad</strong>er Windows ecosystem,” said<br />
Bruce Howe, General Manager for Nokia East<br />
Africa.<br />
The Nokia Lumia 920 includes the latest<br />
<strong>ad</strong>vances in Nokia Pure View imaging<br />
innovation. Using <strong>ad</strong>vanced floating lens<br />
technology, the camera in the Nokia Lumia<br />
920 is able to take in five times more light<br />
than competing smartphones without using<br />
flash, making it possible to capture clear, bright<br />
pictures and video indoors and at night. It<br />
also compensates for hand movement while<br />
the photo is being taken through image<br />
stabilization technology.<br />
In <strong>ad</strong>dition to built-in wireless charging, the<br />
Nokia 920 also comes with Nokia City Lens, the<br />
latest <strong>ad</strong>dition to the Nokia location suite and<br />
the start of a new augmented reality experience<br />
that also enhances Nokia Maps. Along with<br />
enhancements to Nokia Drive and Nokia<br />
Transport, the Nokia location suite of services<br />
represents the most comprehensive, integrated<br />
mapping experience of any smartphone.<br />
The Nokia Lumia 820 is a snappy, mid-range<br />
smartphone that delivers high-end performance<br />
in a compact package. While the Nokia Lumia<br />
820 has the same unibody look and feel as the<br />
high end Lumia smartphones, it comes with an<br />
exchangeable shell design. Exchangeable shells<br />
not only make it possible to select from a range<br />
of colors, but also to <strong>ad</strong>d wireless charging.<br />
Beneath the shell is room to insert a micro SD<br />
memory card.<br />
Both phones will be available in pentaband<br />
LTE and HSPA+ variants.<br />
The Lumia 920 is priced at UGX2, 255,000.<br />
The Lumia 820 is priced at UGX1, 615,000. Both<br />
phones come bundled with 300MB and are<br />
now available at all MTN service centers<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech 9<br />
UPDATE
UPDATE<br />
10<br />
<br />
<br />
<br />
<br />
<br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
Curve 9220<br />
Adobe Creative<br />
Suite 2 goes<br />
free (sort of )<br />
ADOBE, THE CREATOR of software such as Photoshop and<br />
InDesign, has m<strong>ad</strong>e its entire Creative Suite 2 (CS2) free to<br />
downlo<strong>ad</strong> – sort of. Having disabled the CS2 activation servers<br />
late last year, the company was inundated with complaints from<br />
users demanding to downlo<strong>ad</strong> and install software they h<strong>ad</strong> alre<strong>ad</strong>y<br />
paid for. In response, Adobe released both the installation<br />
files and accompanying serial numbers for downlo<strong>ad</strong>, letting<br />
anyone who previously bought CS2 re-install it on a new PC.<br />
However, this generosity has also been extended to the<br />
general public; initially, anyone with an Adobe.com account<br />
was able to downlo<strong>ad</strong> the files, but now simply pointing your<br />
browser at www.<strong>ad</strong>obe.com/downlo<strong>ad</strong>s/cs2_downlo<strong>ad</strong>s/index.<br />
html will give you complete access to the Creative Suite files.<br />
Although the software is only intended for those who purchased<br />
it legally in the past, there’s nothing to stop anyone from<br />
downlo<strong>ad</strong>ing the company’s Photoshop, InDesign, Illustrator,<br />
Premiere, Audition or the entire Creative Suite software to their<br />
own PCs.<br />
CS2 originally launched in 2005, and as such isn’t optimised<br />
for the latest processors or graphics cards – if you want hardware<br />
acceleration and some of the software’s more <strong>ad</strong>vanced<br />
features, you’ll need to pay for the latest version.<br />
However, each application represents a major improvement<br />
over the free alternatives: Photoshop CS2 has many more<br />
features than Microsoft Paint, Paint.NET and the GIMP image<br />
editors, while Premiere is far more powerful than Windows<br />
Movie Maker. InDesign and Illustrator are both industry standard<br />
design programs, which don’t have free alternatives.<br />
We were able to install each Creative Suite application on a<br />
Windows 8 computer and can confirm they work perfectly. It<br />
might be something of a legal grey area, but while the files are<br />
still freely available we suggest you give it a try.<br />
MTN’s cross-border fibre cable commissioned<br />
By AlBert Mucunguzi<br />
MTN Uganda this month commissioned its<br />
fibre network at Katuna Border in Kabale,<br />
Uganda.<br />
“The launch of the new fibre system at<br />
Katuna is a major development which we<br />
are confident will have a positive impact on<br />
the future of Uganda’s ICT Ro<strong>ad</strong>map, and<br />
will substantially improve connectivity with<br />
neighboring countries,” said CEO Mazen<br />
Mroue in a press statement.<br />
The event at Katuna border is has been<br />
graced by ICT Minister, Dr. Ruhakana Rugunda,<br />
UCC‘s Executive Director Godfrey Mutabazi, as<br />
well as MTN Chairman Charles Mbiire.<br />
Since its launch in Uganda in 1998, MTN<br />
Uganda has m<strong>ad</strong>e major investments in<br />
Uganda. In 2012 alone, its CAPEX investments<br />
exceeded USD 80 million by December. This<br />
investment was mainly towards the expansion<br />
of network infrastructure, establishment of<br />
ultra-modern Switching and Data Centre, as<br />
well as rollout of fibre infrastructure to boost<br />
the quality of voice and data services<br />
In terms of Network infrastructure, last year<br />
MTN Uganda rolled out an <strong>ad</strong>ditional 600km<br />
of fibre backbone closing the year with over<br />
2,800km of fibre system providing the capacity<br />
for high speed data connectivity and wider<br />
national coverage of 3G mobile data services<br />
that extend internet access to the rural areas<br />
of Uganda.<br />
MTN Uganda has over the last 6 months<br />
completed the installation of another 81 new<br />
Network Coverage Sites and also <strong>ad</strong>ded<br />
another batch of capacity sites to enhance<br />
the quality of network services across<br />
Uganda. MTN has a total of 1,100 sites at the<br />
end of 2012 providing Network Coverage<br />
and communication services to millions of<br />
Ugandans across the country.<br />
In 2009 MTN Uganda launched the first<br />
mobile money service with tremendous<br />
success. MTN Uganda Mobile Money ranks<br />
2nd in the world in terms of absolute number<br />
of active customer accounts <strong>ad</strong>ded during<br />
2012 as per GSMA research completed<br />
recently.<br />
Over the past couple of years MTN has<br />
also installed backhaul systems providing<br />
connectivity to the submarine cables landed<br />
at Mombasa. This has enabled secured and<br />
reliable connectivity with the rest of the world<br />
while providing quality voice and data services<br />
and high level redundancy.<br />
MTN has an extensive list of new<br />
innovations that will be gr<strong>ad</strong>ually announced<br />
during the year. MTN Uganda announced<br />
recently about the plan to deploy Long Term<br />
Evolution (LTE) network in Uganda during<br />
the coming months, which will enable MTN<br />
Customers to access world class internet with<br />
bandwidth speed up to 100Mbps. Today, more<br />
than 7.5 Million Ugandan enjoys country wide<br />
the Yellow revolution providing best network,<br />
fastest growing Mobile Money services, widest<br />
coverage and world class internet.<br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech 11<br />
UPDATE<br />
Uganda Communications Commissions Executive<br />
Director, godfrey Mutabazi, MTN Chairman Charles<br />
Mbiire, Uganda ICT Minister, Dr. Ruhakana Rugunda,<br />
and MTN CEO Mazen Mroue pose for a photograph at<br />
Katuna border last month. [Photo by A. Mucunguzi]
UPDATE<br />
12<br />
Kenya: SIM Registration<br />
Laws Come Into Effect<br />
The SIM card registration<br />
regulations come into effect<br />
today, a month after they were<br />
gazetted on January 11. The<br />
Communications Commission<br />
of Kenya (CCK) has asked<br />
the operators to submit their<br />
statistics on reconnected lines,<br />
new registrations and suspended<br />
lines to monitor compliance with<br />
the regulations.<br />
Under the Miscellaneous<br />
Amendment Act No 12 of 2012,<br />
mobile operators have to keep<br />
an accurate register of the people they provide<br />
access to. Those found not complying face a<br />
fine of up to KSh500,000 (approx US$5,700)<br />
for any breach of the law.<br />
Users of the unregistered SIM cards are not<br />
spared either as, according to the law, anyone<br />
found in contravention faces a fine of up to<br />
KSh300,000 (approx US$3,400) or a three year<br />
jail term.<br />
MTN, RIM partner on Blackberry 10<br />
MTN Nigeria and Research In<br />
Motion (RIM) - now BlackBerry<br />
- makers of the brand new<br />
Blackberry Z10 smartphone,<br />
are planning to introduce the<br />
new Blackberry 10 to the country. If the deal<br />
sails through, MTN will be the first to bring the<br />
latest Blackberry to the Nigerian market.<br />
MTN customers will be among the first users<br />
in the world to experience the new product,<br />
which has been re-designed to give customers<br />
a unique experience.<br />
Speaking on the deal, Chief Marketing<br />
Officer, MTN Nigeria, Larry Annetts, said the<br />
firm is giving them value for their money.<br />
“MTN is offering pre-order opportunities<br />
thus conferring on our customers the privilege<br />
of being one of the first to own the device in<br />
Nigeria. Not only that, those who pre-order<br />
will get the smartphone at a bargain price and<br />
they will be contacted for pickup at locations<br />
ABOUT PC TECH NEWS<br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
of their choice even before the phones<br />
become commercially available at retail stores.<br />
They are not required to make any deposits;<br />
they will simply pay on delivery,” he said.<br />
MTN Nigeria has an alliance with RIM,<br />
dating back to 2007, when MTN Nigeria was<br />
the first telecoms company in Africa to offer<br />
Blackberry on pre-paid.<br />
Analysts say the success of the Blackberry<br />
10 will largely rest on winning back those<br />
customers who fled for the gorgeous hardware<br />
and exceptional user interface of the iPhone or<br />
fancied the range of phones running Android.<br />
The task is tougher here, though at least<br />
BlackBerry has 70,000 apps available on day<br />
one. This is a remarkable achievement and<br />
is many ways is enough to be going on with.<br />
Apple and Android have over 700,000 apps<br />
each, but the number of jewels is much lower.<br />
Some of the stories posted in this section have been extracted from Pc Tech online’s daily news updates. You can visit www.<br />
pctechmag.com for daily tech news stories. If you wish to run your story, please email it to editor@pctechmagazine.com*.<br />
*Not all stories that we receive are published.<br />
Information<br />
and Communication<br />
ministry permanent secretary Dr<br />
Bitange Ndemo said the efforts are meant<br />
to ensure that a repeat of the 2007/08 post<br />
election violence that saw telecommunication<br />
g<strong>ad</strong>gets play a major role is not repeated.<br />
“Mobile operators will bear<br />
the intermediary liability in that<br />
they become an accomplice by<br />
failure to register the SIM-cards.<br />
Any aggrieved person can sue<br />
the telecommunication firms for<br />
any crimes committed using the<br />
unregistered SIM cards. It will be<br />
upon the mobile operators to<br />
reveal the identity of the person,”<br />
said Ndemo in an interview with<br />
Business Daily.<br />
Critics observe the operators<br />
have every reason to avoid<br />
finding themselves pinned against the wall for<br />
crimes perpetrated by their subscribers given<br />
the number of increased kidnappings and hate<br />
speech using mobile phone devices.<br />
As to the level of compliance, Kenyans have<br />
to wait and see whether the CCK will have the<br />
power to implement some of these threats<br />
against major companies largely considered to<br />
be more powerful than the regulator.<br />
Kenya Begins Construction Of ‘Silicon’ City Konza<br />
Kenya’s president has launched a<br />
$14.5bn (£9.1bn) project to build<br />
a new city intended to be an IT<br />
business hub and dubbed “Africa’s<br />
Silicon Savannah”.<br />
It will take 20 years to build Konza<br />
Technology City about 60km (37 miles) from<br />
the capital, Nairobi.<br />
It is hoped that more than 20,000 IT jobs<br />
will be created in Konza by 2015, and more<br />
than 200,000 jobs by 2030.<br />
Despite Kenya’s usually divisive politics, the<br />
project has the backing of all political parties.<br />
Konza is part of the government’s ambitious<br />
Vision 2030 initiative to improve muchneglected<br />
infrastructure over the next 18<br />
years.<br />
Correspondents say the government also<br />
wants to take <strong>ad</strong>vantage of the growing<br />
number of software developers in the East<br />
African nation.<br />
‘TREMENDOUS OPPORTUNITIES’<br />
“It is expected to spur massive tr<strong>ad</strong>e and<br />
investment as well as create thousands of<br />
employment opportunities for young Kenyans<br />
in the ICT [information communications<br />
technology] sector,” President Mwai Kibaki said<br />
at the ceremony to launch the construction,<br />
<strong>ad</strong>ding it would be a “game-changer” for the<br />
country’s development.<br />
He called on domestic and foreign investors<br />
to take <strong>ad</strong>vantage of Konza’s “tremendous<br />
opportunities”.<br />
The 5,000-acre (2,011-hectare) site was a<br />
ranch to the south-east of Nairobi on the way<br />
to the port city of Mombasa.<br />
When the plan was announced after the last<br />
elections property prices in the area soared,<br />
reporters say.<br />
According to the Konza information<br />
website, the city wants to attract business<br />
process outsourcing, software development,<br />
data centres, disaster recovery centres, call<br />
centres and light assembly manufacturing<br />
industries.<br />
A university campus focused on research<br />
and technology as well as hotels, residential<br />
areas, schools and hospitals will also be built.<br />
The government has appointed the Konza<br />
Technopolis Development Authority to oversee<br />
the building of the IT hub, which will be built<br />
in four phases – starting with the technology<br />
centres first.<br />
NaiLab has been contracted by the Kenya<br />
ICT Board (KICTB) to pilot the National<br />
Business Incubation program for companies<br />
with high growth potential. This project is an<br />
initiative of the Kenyan Ministry of Information<br />
and Communications under the World Bank<br />
funded Kenya Transparency & Infrastructure<br />
Project.<br />
NaiLab is a Kenyan Tech Business Incubator<br />
based in Nairobi that was launched two years<br />
ago. It’s goal is to lower the entry barriers for<br />
ICT entrepreneurs who want to start and scale<br />
their businesses in Kenya. Business Incubation<br />
provides entrepreneurs with access to critical<br />
information, education, contacts, capital and<br />
other resources crucial to the growth of the<br />
business.<br />
Ten tech ways to say ‘I love you’<br />
1. TWEET YOUR SWEET CLUES TO WHERE<br />
you should meet with Google Map links and<br />
send her Facebook gifts as a prelude to more<br />
geeky treats. Tech her out to a laser show<br />
and have her select whether she likes the Jelly<br />
Bean, Gingerbre<strong>ad</strong> or Ice Cream Sandwich<br />
as a Valentines gift. As the final move, show<br />
her a YouTube link to your love declaration<br />
and leave her a self-designed game where<br />
the hero rescues the damsel in distress from a<br />
world being overtaken by killer robots.<br />
2. Give your girl a bunch of roses, handm<strong>ad</strong>e<br />
via your 3D printer.<br />
3. For those struggling to find someone to<br />
tell those three special words, check out the<br />
Crazy Blind Date app, powered by developers<br />
OKCupid. Unlike other dating applications, it is<br />
more private and turns dating into a game. All<br />
the user gets prior to the date is a scrambled<br />
picture of their potential love interest.<br />
4. Will you embed with me?<br />
5. The free Valentine app for Windows<br />
Phone does the job for you with a gift section<br />
and 40 pre-designed romantic text messages.<br />
All you need to do is enter the right number.<br />
6. Poke them on Facebook.<br />
8. If there is no one to say ‘I love you’ to<br />
then check out new South African social network<br />
No Strings Attached. A “hookup” website<br />
which went live on January 4, it is free for the<br />
first two months after registration. The site is<br />
based on the premise that people do not want<br />
relationships, but rather a ‘one night-stand’.<br />
9. Rather than tell a person ‘I love you’,<br />
Where is Your Valentine allows people to label<br />
a place their one true love. Developer team<br />
Maptia believe “places are like people - that<br />
their sights, and sounds, and personalities can<br />
fill our lives with joy and wonder, that we can<br />
fall he<strong>ad</strong>s over heels in love with a place just<br />
as deeply as with a person, and that for just<br />
a few special places we form relationships or<br />
memories that last a lifetime”.<br />
10. Nestor Benavidez: Why not use a programming<br />
language to say ‘I love you’?:<br />
a) Java comment<br />
/* I love you */<br />
b) Ruby times loop<br />
1000000.times do<br />
puts “I love you”<br />
end<br />
c) Java while loop (infinite)<br />
while (true)<br />
{<br />
IloveYou++;<br />
}<br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech <strong>13</strong><br />
UPDATE
WHAT’S NEW<br />
gADgETS, TECHNOLOgY<br />
14<br />
BlackBerry’s<br />
Z10 Smartphone<br />
BLACKBERRY Z10 ISN’T JUST<br />
another new smartphone. It’s a<br />
symbol of redemption, the net<br />
result of the efforts of thousands<br />
working to salvage one of the most<br />
famous brands in the history of<br />
mobile technology. For the first<br />
time in years, “the new BlackBerry”<br />
isn’t just some repackaged business<br />
phone; it’s an iconic flagship on<br />
which rests the fate of the company<br />
that now shares its name.<br />
“We h<strong>ad</strong> to make a serious<br />
decision,” BlackBerry CEO Thorsten<br />
Heins said at the coming-out party<br />
for its new smartphones; “<strong>ad</strong>opt<br />
someone else’s platform, or build a<br />
new one from the ground up. We<br />
decided to go it alone.”<br />
It’s almost easier to ask “what<br />
changes weren’t m<strong>ad</strong>e?” This is a<br />
ground-up overhaul for BlackBerry,<br />
and they’re hedging the entire<br />
company on the success of this<br />
new platform. Among some<br />
improvements:<br />
•<br />
The Z10’s hardware is a giant<br />
step forward. It packs a 1.5<br />
GHz dual-core Snapdragon S4<br />
CPU, 4.2-inch HD display, 2 GB<br />
THE PROTOTYPE PANASONIC 4K 20-inch tablet<br />
premiered at CES 20<strong>13</strong> in Las Vegas. But it won’<br />
remain a prototype for much longer. Yup, this megasize,<br />
ultra HD tablet is he<strong>ad</strong>ing to the shelves later in<br />
the year.<br />
Aimed at the pro market, the giganta-tab - which<br />
doesn’t have an official name or price point as yet<br />
- packs in a 3840 x 2560 pixel resolution across its<br />
20-inch LED-backlit surface. But it doesn’t <strong>ad</strong>d on the<br />
pounds. Weighing in at around 2.2kgs, it feels really<br />
light considering its sheer scale.<br />
Tucked in to the trim body is an Intel Core i5<br />
1.8Ghz processor with Nvidia GeForce graphics and<br />
16GB of RAM and a 128GB SSD for storage. We h<strong>ad</strong><br />
a play with the Windows 8 touchscreen and all that<br />
power sure does deliver the heat - literally; the rear of<br />
the tablet felt very warm to the touch when rested on<br />
the one hand.<br />
The touchscreen felt generally responsive and we<br />
even h<strong>ad</strong> a play with an optional stylus that responded<br />
much like a normal pen. Writing, scribbling - it was<br />
easy to <strong>ad</strong>d notes over architectural drawings.<br />
Visually, too, the 4K tablet with its relatively slight<br />
bezel is all about the visuals. Flicking through a gallery<br />
•<br />
•<br />
•<br />
of RAM, a 1,800 mAh battery,<br />
and 4G LTE connectivity (in<br />
most markets). The hardware<br />
itself is well-designed, and<br />
still retains a corporate look<br />
and feel for those legacy<br />
BlackBerry users.<br />
The camera is improved<br />
and offers new features like<br />
TimeShift, which allows you<br />
to take multiple pictures and<br />
choose the best face(s) - all<br />
without modifying the existing<br />
picture.<br />
The on-screen keyboard is<br />
a huge improvement from<br />
the Storm days, with fantastic<br />
prediction software.<br />
BlackBerry 10 exudes a far<br />
more modern feel, though the<br />
exact gestures will take some<br />
time to get used to. The<br />
personalization isn’t quite to<br />
par with other OSes on the<br />
market, and the file system<br />
needs some work.<br />
It’s new! For those fatigued with<br />
Android, iOS, and Windows Phone,<br />
this could be a device to turn<br />
to.<br />
of Lumix camera images the resolution and bright<br />
panel really shows its worth.<br />
How much, exactly, that will be worth we’re yet to<br />
hear. Don’t expect this tablet to be a budget buy by<br />
any means, but we’re impressed with what’s on ground<br />
so far.<br />
Google’s Touchscreen Laptop<br />
The Chrome Pixel<br />
GOOGLE unveiled a groundbreaking<br />
new Chromebook laptop — one with<br />
touchscreen capability,<br />
powerful chipset<br />
and an extremely<br />
high-resolution<br />
display.<br />
The Chromebook<br />
Pixel, available for<br />
order on the Google Play<br />
store and shipping in April,<br />
features a 12.85-inch touchsensitive<br />
Gorilla Glass screen.<br />
The resolution is 4.3 million pixels,<br />
which<br />
works<br />
out to<br />
239<br />
pixels per<br />
inch. (The average Windows<br />
laptop has about half that; technically, it also<br />
beats the Macbook Retina.)<br />
The Pixel will come in two versions, both<br />
boasting an Intel Core i5 processor. The<br />
basic model is Wi-Fi only; a more expensive<br />
model has the ability to connect to Verizon’s<br />
superfast LTE network. Google claims a battery<br />
life of five hours on the device, which has<br />
QuickOffice built into the browser and an<br />
SD card slot for automatic photo uplo<strong>ad</strong>s to<br />
Google+. Those features can also be used<br />
offline<br />
(uplo<strong>ad</strong>s queued for<br />
later, of course).<br />
The price, however, is relatively steep:<br />
$1,299 for the Wi-Fi only version, $1,449 for<br />
the LTE model.<br />
Google was careful to emphasize that the<br />
Pixel isn’t for everyone. “This is for power users<br />
who live in the cloud,” Senior Vice President of<br />
Chrome Sundar Pichai repeatedly told a select<br />
group of journalists at a low-key launch event<br />
in San Francisco.<br />
Having a touchscreen doesn’t mean that<br />
Google plans to integrate its mobile OS,<br />
Android, into the device. But Pichai hoped<br />
web developers would start making their<br />
interfaces touch-sensitive — so that content<br />
on the device would be indistinguishable from<br />
Android.<br />
“Touch is here to stay, and I’m pretty sure<br />
every laptop will have touch in the future,”<br />
Pichai said. “Using a laptop with touch seems<br />
strange at first, but your day-to-day browser<br />
experience starts changing. In our tests,<br />
users started replacing the touchp<strong>ad</strong> pretty<br />
quickly.”<br />
The aluminum-coated Pixel was designed<br />
and built by<br />
Google, with help from<br />
other unnamed PC manufacturers. Plenty of<br />
thought appears to have gone into the design:<br />
For example, there’s an extra laser microphone<br />
under the keyboard, complementing the two<br />
mics next to the camera, allowing the software<br />
to cancel out any noise you might make while<br />
typing on a video conference.<br />
“Our goal was to have the hardware<br />
disappear,” Pichai <strong>ad</strong>ded.<br />
Panasonic 4K 20-inch tablet New Samsung Refrigerator<br />
Has Soda Stream Built In<br />
We’ve seen some pretty snazzy high tech<br />
refrigerators lately, but a fridge that has a<br />
sparkling water dispenser? That takes the<br />
cake.<br />
Samsung has announced that its new 36”<br />
four-door refrigerator has the industry’s firstever<br />
automatic sparkling water dispenser.<br />
It’s powered by SodaStream, so you can get<br />
cold, bubbly water anytime of the day or<br />
night. The filtered sparkling water will come<br />
through the dispenser on the fridge door<br />
that alre<strong>ad</strong>y delivers water and ice.<br />
The sparkling water dispenser uses a<br />
standard SodaStream 60L CO2 cylinder<br />
which is concealed inside the left refrigerator<br />
door. That way it’s easy to get to when you<br />
need to change it.<br />
Kevin Dexter, senior vice president of<br />
home appliances sales and marketing for<br />
Samsung Electronics America, said, “By<br />
joining forces with SodaStream, we are able<br />
to offer our consumers something never<br />
before seen on a refrigerator and bring a<br />
new experience to the kitchen.”<br />
All this fizz comes with a price.<br />
The Samsung Refrigerator with sparkling<br />
water dispenser will be available in the U.S. in<br />
April 20<strong>13</strong> for around $3899.<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
WHAT’S NEW 15
COVER STORY<br />
16<br />
Inside East<br />
Africa’s Biggest<br />
Co-working<br />
Spaces<br />
“Hubs” are all over the place these days. And if you look closely,<br />
it means there’s one universal problem: how to turn techies into<br />
entreprenuers. So this article, part of which is from a report from<br />
a research that used iHub (Nairobi) as a case study, seeks to tell<br />
us how the business of coding is turning into real business!<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
COVER STORY 17
COVER STORY<br />
18<br />
DOWN TO BUSINESS<br />
As fibre optic cables continue to lay the<br />
foundations for a new era of African innovation,<br />
the continent is undergoing a dramatic “techhub<br />
boom”. There are now more than 50 tech<br />
hubs, labs, incubators and accelerators across<br />
Africa, with a new one springing up nearly<br />
every two weeks.<br />
These hubs portray a very different Africa<br />
to the one often seen in the media and attract<br />
creative, young tech gr<strong>ad</strong>uates who come in<br />
search of opportunity. In most cities, these<br />
spaces offer students, programmers, developers,<br />
entrepreneurs, creative, investors and techies a<br />
place to work, network and create for the first<br />
time.<br />
As these spaces become the nerve centres<br />
for the tech community, they also become<br />
critical international touch-points for those<br />
seeking to engage in technology and business in<br />
Africa. They are the new points of exchange for<br />
long-term expatriates and short-term visitors<br />
looking to identify trends, find local talent, and<br />
catch the African wave of innovation.<br />
AS<br />
part of a year-long<br />
study on various ICT<br />
Hubs across Africa,<br />
the iHub Research<br />
conducted a 3-month<br />
study to understand the iHub model, its<br />
members and how the iHub impacts the<br />
individual members. The study builds on<br />
surveys with the 7,011 total members and<br />
interviews with various stakeholders.<br />
This research aimed to understand the<br />
impact of the ICT Hubs to entrepreneurs.<br />
An ICT hub is a space where technologists<br />
congregate to bounce ideas around, network,<br />
work, program and design to bring their ideas<br />
to fruition. The first ICT Hub of the 15 hubs<br />
to be profiled within this study series is iHub,<br />
Nairobi’s innovation Hub for the Technology<br />
Community. The study found that 100% of<br />
the entrepreneurs appreciate the iHub space<br />
as it has been a conducive and innovative<br />
co-working space that drives continuous<br />
networking through the events, community<br />
meetups that le<strong>ad</strong>s to collaboration and<br />
partnerships, sharing skills and knowledge<br />
through teamwork among others. This is likely<br />
because most of these talented entrepreneurs<br />
having gr<strong>ad</strong>uated with no formal job<br />
opportunities, have h<strong>ad</strong> their talents and<br />
skills nurtured and housed under these hubs.<br />
Overall, the entrepreneurs believe that the<br />
iHub can further sustain this co-working spirit<br />
by building more capacity through communal<br />
projects and active virtual member interaction<br />
among others.<br />
ABOUT IHUB<br />
For years, technological innovations were<br />
limited to universities and to a select few<br />
ambitious souls. In the span of two to<br />
three years, however, the innovation scene<br />
in Kenya has greatly expanded thanks to<br />
careful planning and a push for a robust<br />
telecommunications infrastructure and highcapacity<br />
International gateways. At the front<br />
line, pushing for this progress has been the<br />
Kenya ICT Board.<br />
The Kenya ICT Board aims to accelerate the<br />
momentum of the ICT sector in the country.<br />
Dr. Bitange Ndemo, the Permanent<br />
Secretary in the Ministry of Information and<br />
Communications has conceptualized a plan<br />
to see ICT contribute twenty-five percent to<br />
the country’s gross domestic product (GDP) –<br />
which would out<strong>strip</strong> agriculture’s contribution<br />
to GDP in the country (ICT Procurement 2012).<br />
The Kenyan government also plans to set up<br />
a steering committee to oversee the country’s<br />
transition to a “digital nation,” providing<br />
support to entrepreneurs looking to start their<br />
own businesses.<br />
There is huge untapped talent of young and<br />
upcoming tech innovators who are building<br />
great innovations (Vision 2030 Report Kenya).<br />
Hubs such as iHub are being viewed by many<br />
as a means of nurturing talent and providing<br />
youth employment for gr<strong>ad</strong>uates. It is<br />
therefore important to understand what makes<br />
these Hubs/Labs successful and their impact<br />
to the tech community of entrepreneurs.<br />
This understanding is recommended for the<br />
successful implementation of ICT Hubs.<br />
A recent article written on ‘Silicon Valley<br />
of the World’ by IBM SmartCamp, that<br />
examines the world’s up-and-coming tech<br />
communities – from Germany to Mexico<br />
to Indonesia and more – compare them<br />
on a number of different factors, including<br />
entrepreneurial mindset, access to capital and<br />
general strengths and weaknesses shows that<br />
the global entrepreneurship index is at 2.49:<br />
Kenya is at 2.63, second only to Nigeria at 2.7<br />
in Africa among others like the US at 2.8.<br />
This number clearly depicts the great<br />
potential for Kenya to become a globally<br />
recognized ICT center and more so, an<br />
environment for nurturing entrepreneurs<br />
talent to a higher level. Entrepreneurship<br />
is becoming widely recognized for its<br />
role in economic growth through youth<br />
employment to solve problems that improve<br />
the living standards of the community to<br />
enhance a common goal hence need for<br />
more research to be done on tech hubs to<br />
understand the implementation of the models<br />
and entrepreneurs to ensure a sustainable<br />
SOCIAL SPACE: The hubs are not just about work. They also act as focal<br />
point for the tech community to come together, learn and, of course party.<br />
approach in the making.<br />
As part of a year-long study on various<br />
ICT Hubs across Africa, the iHub Research<br />
conducted a 3-month study to understand the<br />
iHub model, its members and how the iHub<br />
impacts the individual members. This report<br />
is the second phase of the first report in the<br />
series, after the first phase that examined the<br />
ICT Hubs model report of the iHub, which<br />
explains how the iHub and its management<br />
model works. The two reports are<br />
complementary to each other and together<br />
inform the re<strong>ad</strong>er of the various components<br />
of the iHub, how they are managed and<br />
how its management model impacts its<br />
entrepreneurs.<br />
To access the iHub Model report, go to<br />
http://bit.ly/JtonRl.<br />
Currently there are 7,011 total members in the<br />
iHub in all membership tiers. 5,915 (84%) are<br />
male and 1,096 (16%) are female.<br />
The noticeably large gap in male and<br />
female members of the iHub reflects a larger<br />
countrywide and global trend. The gender<br />
gap in technology remains very real across<br />
the world, including in Kenya. Perhaps the gap<br />
exists because women view computer science<br />
as a subject for men, or have not developed<br />
skills in the field because they have not been<br />
exposed to the subject matter or have been<br />
discouraged by family and friends. Despite the<br />
many possible analogies why there are fewer<br />
women in the computer science field, there is<br />
enormous potential for maximizing the growth<br />
of technology through increasing the number<br />
and quality of women in technology with<br />
initiatives such as Akirachix among others that<br />
are springing up from the iHub.<br />
HOW IHUB STARTED<br />
iHub was started as part of the Ushahidi<br />
strategy. Erik Hersman, founder of iHub, and<br />
a group of young developers, volunteers and<br />
journalists who were passionate and energetic<br />
about technology assisted in developing the<br />
Ushahidi platform for the global community.<br />
Due to space limitation, the developers<br />
were forced to meet in co_ee shops and<br />
restaurants that h<strong>ad</strong> limited WiFi connection.<br />
These meeting places h<strong>ad</strong> a couple of<br />
challenges.<br />
It was expensive for the members to work<br />
from there, as they h<strong>ad</strong> to buy something to<br />
either eat or drink as they worked from places<br />
like Java House and Dorman’s.<br />
There were also many distractions that<br />
arose from the restaurants.<br />
It was then that, Erik Hersman, some of<br />
the <strong>ad</strong>visors, and Jessica Colaço, the initial<br />
iHub Manager; gave birth to the iHub—at<br />
the time, just a bare concrete space with a<br />
few chairs, a table, and a router flickering<br />
in the background. The original team sat<br />
and thought of how they would be able to<br />
accommodate thousands of techies in Nairobi<br />
in that space and breathe life into the space<br />
and the community. “We were looking for<br />
techies who were doers and not talkers. The<br />
techies therefore h<strong>ad</strong> to undergo a vetting<br />
process and fit within a certain structure,” says<br />
Jessica Colaco. “We then decided to come up<br />
with a membership structure to accommodate<br />
the physical and virtual techies of Nairobi and<br />
Kenya,” she continues.<br />
Erik started jotting the structure that the<br />
iHub would <strong>ad</strong>opt on a piece of paper. White<br />
members – these are the ‘virtual’, green<br />
members – those who can physically access<br />
the space, red members - physical members<br />
with a semi-permanent desk space, and black<br />
members - the iHub management team that<br />
assists in daily management and operations.<br />
All of these members came together to<br />
make the iHub space a reality. It was only later<br />
that the founding team realized that they h<strong>ad</strong><br />
picked the colors of the Kenyan flag for the<br />
membership structure.<br />
The piece of paper, which h<strong>ad</strong> the details of<br />
the membership structure, was then used to<br />
develop wireframes and mockups to be used<br />
to build the iHub membership system.<br />
These were further refined to a functional<br />
website by a volunteer web team, led by<br />
Joshua Musua, the webmaster for iHub.<br />
Challenges faced by members as they run<br />
their businesses<br />
The entrepreneurs have also faced<br />
challenges either as startups or freelancers<br />
Inside kLab, Kigali<br />
Expectations while joining kLab<br />
When coming to kLab, there is one thing in mind, a space to think and collaborate. My<br />
expectation in the space was to find people that could work within our startup company<br />
Zilencio Creativo’s project and bring it to life. Coming from a technical background with a<br />
passion for branding I needed people with programming skills to team up with so that we<br />
harness our efforts and create an impactful product.<br />
kLab environment and culture<br />
kLab is a serene environment for developers, IT enthusiasts and interested parties of a growing<br />
ICT community in Rwanda fostering intellect and entrepreneurial spirit. “The space gives<br />
one a peace of mind to work, providing a professional space to engage with other tenants and<br />
experienced mentors” says Ara.<br />
kLab brings like-minded innovators together and give them the resources they need<br />
to explore their ideas, learn from each other, and develop innovative solutions. kLab is<br />
a technology space enabling ambitious entrepreneurs come together and develop their<br />
trailblazing ideas into successful businesses.<br />
Opportunities and exposure at kLab<br />
Ara’s startup company, Zilencio Creativo emerged as the 2012 finalist for the Startup World<br />
competition in Kigali. “As we prepare ourselves to travel to Sillicon Valley to compete globally,<br />
we are working hard on our winning crowdfunding project prototype” says Ara. My company<br />
was also selected to be part of local ICT companies that went to showcase their products at this<br />
year’s ITU Telecom World in Dubai, with this our team considers this opportunity and award<br />
possible only by the exposure provided by kLab.<br />
With people you create experiences; kLab is such a space to provide you with both an<br />
experience and a community to engage with. For any technology person out there, for<br />
any person who has an idea that can get into the ICT field, I recommend to join the kLab<br />
community.<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
COVER STORY 19
COVER STORY<br />
20<br />
DOWN TO BUSINESS<br />
as they run their businesses. Some of the<br />
key challenges that the researchers identified<br />
include but not limited to:<br />
1. Funding<br />
Many of the entrepreneurs either have<br />
no access to enough capital to grow their<br />
business in terms of scaling up their products<br />
and their team capacity, hence many of<br />
them do not end up focusing on their core<br />
business, but are required to have free-lance<br />
side projects in order to generate revenue<br />
to sustain the business. Without appropriate<br />
financing, the inevitable result is a significant<br />
slowdown in the business development<br />
process, which may ultimately jeopardize<br />
chances of success.<br />
2. Sustained Growth<br />
With today’s increased market competition<br />
and change of technologies, requires that<br />
the entrepreneurs need to constantly revise<br />
their innovation strategy by continuously<br />
developing and organizing capabilities<br />
within companies and translating them into<br />
competitive <strong>ad</strong>vantages and profits. The<br />
challenge faced by most of these startups is<br />
the ability to continuously innovate to cultivate<br />
the right environment where their innovations<br />
can be repeated and satisfy the needs of the<br />
existing customers.<br />
3. The right mentors<br />
Only a few of the entrepreneurs are lucky<br />
enough to have the support of mentors. Many<br />
of these entrepreneurs are still searching for<br />
the right mentors who can create time to<br />
continuously <strong>ad</strong>vise them and guide them<br />
through as they run their business. Mentors<br />
come in di_erent shape, size and forms, with<br />
their experience and diverse skills they can be<br />
able to strategically provide support that is<br />
necessary to the entrepreneurs in each stage<br />
of their business. Finding a good mentor and<br />
building a strong relationship takes time. It<br />
takes a strong time investment on both sides<br />
in order to make it a meaningful and valuable<br />
relationship.<br />
4. Pricing their products<br />
Q&A: Outbox Hub’s Richard Zulu<br />
TELL US ABOUT OUTBOx<br />
Outbox is a technology incubation, collaboration<br />
space, and innovation hub for techies – as well<br />
as other people in the technology space to meet<br />
and create ideas that they can later on turn<br />
into sustainable businesses that utilize a mobile<br />
phone and the internet.<br />
Those are the three aspects of Outbox. So,<br />
first of all, we focus on fostering technology<br />
entrepreneurship – which we do through the<br />
incubation of utmost 5 startups in our incubation<br />
program. We take these through business and<br />
technology training, thereby helping them<br />
become sustainable businesses.<br />
As far as Collaboration is concerned, we<br />
create a space where like-minded people can<br />
come together can co-create. You see, when<br />
businesses thrive, there’s also a possibility of<br />
inter-marketing, because of the various skills<br />
that these individuals have. All that boosts<br />
entrepreneurship. That’s done through the space,<br />
and also the kind of events that we hold.<br />
Our main focus is entrepreneurship, but not<br />
everybody is born to be an entrepreneur. Which<br />
brings me to our third aspect, Capacity Building.<br />
We engage with different groups in various<br />
events through which we equip them with skills<br />
we believe can empower them to perform better<br />
in their various fields. We hosted over 20 events<br />
last year alone.<br />
We’ve been able to work and take in three<br />
companies – startups – and last year one of<br />
them was able to obtain funding to help them<br />
set up.<br />
HOW SIGNIFICANT IS THE<br />
FUNDING?<br />
It’s very significant. Quite a lot.<br />
WHICH COMpANY IS THAT?<br />
Unfortunately, I can’t disclose.<br />
HOW DOeS OUTBOx BeNeFIT?<br />
At the end of the day, we want to have<br />
impact. Our current focus is to create<br />
sustainable businesses that drive relevance on<br />
the mobile and web. Having such milestones will<br />
encourage other people to embrace the kind of<br />
initiatives that we are trying to push out here – it<br />
le<strong>ad</strong>s us more to our final objective.<br />
HOW DO YOU SUSTAIN YOUR ACTIVITIeS?<br />
Outbox’s sustainability model is built around quite<br />
a number of things. First of all, Outbox provides<br />
the co-working space – a space that comes at a<br />
price. entrepreneurs pay to have access to the<br />
internet, access to our partner network – Google,<br />
Samsung, e.t.c - and access to our business<br />
support services.<br />
We also host a number of events – people rent<br />
the premises to host various events.<br />
Outbox is run as a business.<br />
BUT YOU HAVe pARTNeRS WHO ARe<br />
GIVING YOU SeeD FUNDING; HOW DO THeY<br />
BeNeFIT FROM YOUR ACTIVITIeS?<br />
Most of the partners we work with align with<br />
the objective of creating sustainable businesses,<br />
and that’s how we look out for our partners.<br />
Working with such an initiative helps them push<br />
their objectives as we achieve ours. Having all of<br />
us working together in the ecosystem will later<br />
on help us realize our goals.<br />
YOU’Ve HeARD OF THe LAW OF<br />
DIFFUSION OF INNOVATION? HOW DOeS<br />
THIS FIT INTO YOUR BUSINeSS pLAN?<br />
One thing we have realized is that it’s still a<br />
challenge for most of the people to understand<br />
what we do. When you talk of words like<br />
Innovation, collaboration – some people don’t<br />
quite understand what we do.<br />
Most of the people we have in this space are<br />
early <strong>ad</strong>opters – people who go out of their way<br />
to learn what it is that’s going on here.<br />
The kind of marketing we do is mainly<br />
through out-reach activities – universities and the<br />
like. Our approach to outreach is very targeted,<br />
and we have intentionally kept it that way.<br />
It is clear that 77% of the<br />
entrepreneurs we interviewed have clients<br />
for their business, but the question is are<br />
they proposing the right prices to them?<br />
How do they ensure they price their products<br />
sustainably and not ‘free’ model that will le<strong>ad</strong><br />
their companies to bankruptcy? On the other<br />
hand, if the entrepreneurs are working on<br />
social products, do they have enough support<br />
from funders to scale their products? Most of<br />
the entrepreneurs do not consider coming<br />
up with a pricing strategy for their products,<br />
basing their pricing on tiers depending on<br />
their target users.<br />
5. Competition<br />
The entrepreneurs competing against larger<br />
organizations in the market such as Google,<br />
and Safaricom, among others, sometimes<br />
find that their ideas end up being ‘stolen’<br />
and implemented by these corporates. This<br />
le<strong>ad</strong>s to the entrepreneurs having a negative<br />
mindset and lack of confidence in their ideas.<br />
They end up having excuses, fears that<br />
paralyze them from achieving their dream.<br />
6. Unverified Assumptions<br />
The nexus of tech startup failures are false<br />
assumptions, wild guesses, conjecture and<br />
generalized self-deception. Extrapolating<br />
anomalies are in the same category as false<br />
assumptions. Most of the entrepreneurs do<br />
not consider doing market research before or<br />
as they develop their projects to understand<br />
their market and if their product is viable.<br />
They focus on the technical aspect and forget<br />
the most important thing that clients want to<br />
know —how does this technology, product or<br />
service <strong>ad</strong>d value to me? How does it solve<br />
my problem?<br />
WHITE MEMBERS<br />
Richard zulu,<br />
Program Director<br />
- Outbox Uganda<br />
As earlier mentioned, the iHub has a<br />
population of 7,011 members. As it is<br />
impossible to have all of these members<br />
physically accessing the space, 96% of the<br />
entire iHub membership populations are<br />
white members (6,738 in number). The white<br />
members are basically an online community<br />
that attends occasionally or regularly the iHub<br />
events held in the physical space. These white<br />
members are constrained by various factors<br />
that do not allow them the option of being a<br />
red or green member as depicted in the figure<br />
below:<br />
RECOMMENDATIONS<br />
The key objectives of the research was to<br />
investigate what factors make up the ICT Hubs<br />
model and how the model itself impacts to<br />
the entrepreneurs in the space, that make<br />
them to actively continue to use the space. In<br />
the coming months, the study will also focus<br />
on other initiatives in the eco-system such<br />
as innovations at high level of education and<br />
upcoming local tech companies’ in order to<br />
measure the innovation in the country, which<br />
will then be replicated to other hubs, and<br />
initiatives around Africa.<br />
In the long run the research will aim to do<br />
a comparative study to identify what unique<br />
factors came out of the different hubs that<br />
make them successful creating an impaction<br />
on the economy’s development that is<br />
<strong>ad</strong>option of new technologies and innovations<br />
of employment le<strong>ad</strong>ing to improvement in the<br />
living standards.<br />
RECOMMENDATIONS FOR IHUB<br />
AND OTHER ICT HUBS:<br />
When asked what changes members<br />
would like to see at the iHub this year<br />
(2012), members shared the following<br />
recommendations:<br />
Events to Build Pitching and Presentation<br />
Skills<br />
30% (n=6) of the interviewed members<br />
suggested that the iHub management should<br />
train people on pitching their products.<br />
The researchers believe that eff¬ecting<br />
platforms such as 5-minute presentations<br />
with the overall community, and community<br />
consulting projects will greatly accelerate<br />
the development of members’ skills through<br />
sharing knowledge, above all building<br />
members’ confidence to become better in<br />
presentation skills.<br />
Creating Opportunities For Funding<br />
the iHub management to start marketing startups<br />
that have a good product to potential<br />
investors and clients, also creating formal<br />
networks for seed funding opportunities.<br />
Finding relevant funding for startups has been<br />
a key challenge at their early stages (Capital<br />
Markets Authority of Kenya 2012), although<br />
some innovators and entrepreneurs have<br />
found avenues to get the funding they need<br />
through participating in pitching competitions<br />
such as IPO48, Pivot East, and Mobile Garage,<br />
among others.<br />
Hence there is a need for ICT Hubs to<br />
help start-ups look for necessary funding<br />
from a wide array of sources, such as using<br />
venture capitalist from their networks but also<br />
<strong>ad</strong>vocating for more local investors to start<br />
investing in making the country an IT hub. On<br />
the other hand, the entrepreneurs have to be<br />
serious about their businesses and execute to<br />
enhance minimal risks and an incentive for the<br />
investors to see the startup succeed; the better<br />
the startup does, the greater the Venture<br />
Capitalists’ return on investment.<br />
Diversity of Events<br />
This study revealed that there are some<br />
members who frequent the space often feel<br />
the iHub events are repetitive. Nevertheless,<br />
these responses are not reflective of all of the<br />
7,011-iHub members. The research suggests<br />
that iHub management not to eliminate the<br />
events that are currently taking place, but<br />
rather, have more diversified events, especially<br />
focused on business aspects of building a<br />
start-up. In <strong>ad</strong>dition, exploring other avenues<br />
of marketing the events may also help to bring<br />
new audience groups to the iHub events.<br />
Membership Turnover<br />
Having a 6-month assessment for green<br />
members to reapply for membership allows<br />
other members a chance to apply and<br />
enjoy the benefits of the iHub space. White<br />
members who are virtual should be given<br />
alternative options depending on their<br />
schedule, even if it means allowing them<br />
to visit the space and work for some hours<br />
to physically interact with the community.<br />
Nevertheless, the researchers believe having<br />
online forums and initiatives such as the online<br />
write board will be a remedy for physical<br />
engagement with the community.<br />
RECOMMENDATIONS FOR<br />
ENTREPRENEURS:<br />
Create a detailed financial model<br />
Members suggested that it would be good for<br />
Want to contribute to PC Tech Magazine?<br />
Contact us with a brief bio, and a link to your previous pieces<br />
editor@pctechmagazine.com<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
COVER STORY 21
SPECIAL<br />
22<br />
Bootstrapping–self-funding from one’s own savings such as<br />
pocket money, friends & relatives—is the most preferred option<br />
for funding a start-up because one does not end up spending a<br />
lot of time going hat-in-hand to investors and does not relinquish<br />
any control of their company. Entrepreneurs should ensure they<br />
have carefully planned their businesses in <strong>ad</strong>vance by creating a<br />
detailed financial model that projects their revenues accurately,<br />
estimating the company’s financial circumstances over the next<br />
2-3 years.<br />
ICT Hubs should also set up formal mechanisms to link<br />
entrepreneurs to potential capital opportunities through venture<br />
capitalists or funding to promote their own innovators.<br />
Create a strategic plan<br />
The challenge of most of the startups is to continuously innovate<br />
and cultivate an environment where innovations can be repeated<br />
and satisfy the needs of customers. This challenge can be<br />
<strong>ad</strong>dressed through a clear strategic plan where the entrepreneurs<br />
can continuously revise to always ensure they align with the<br />
changing needs of their users and changing technologies.<br />
Creating and implementing a clear strategy will not only set the<br />
company on a clearly articulated course to growth but also bring<br />
positive side effects like improving teamwork and boost morale.<br />
Find Appropriate Mentors<br />
No man is an island, and every entrepreneur needs guidance<br />
and a support network. While it is important to have a network<br />
of friends, collaborators, and connections from the community,<br />
it is equally important to have a mentor act as a steward for the<br />
startup. Mentors can assist a start-up think through the business<br />
idea, suggest ways to get funding, or provide the experience and<br />
contacts that a young business needs.<br />
Finding the right mentor is a hard task for entrepreneurs,<br />
something that the management of ICT Hubs can work out<br />
through their networks, compiling a reliable pool of mentors,<br />
which entrepreneurs can tap into for help.<br />
Plan your products accurately<br />
Entrepreneurs need to formulate a pricing strategy as they plan<br />
their business. A pricing strategy will help entrepreneurs to<br />
structure their prices based on their users. Entrepreneurs also<br />
need to seek <strong>ad</strong>vice from experts or mentors to <strong>ad</strong>vise if their<br />
pricing model makes sense. Finally, entrepreneurs must research<br />
the offering of their competitors and compare prices in order to<br />
remain competitive.<br />
Conduct Market Research to Test Your Assumptions<br />
New facts and circumstances can change the validity of any<br />
assumption previously held. S<strong>ad</strong>ly, the management of some<br />
tech start-ups continue to rely upon original assumptions, despite<br />
mounting results and financial evidence to the contrary. Verifying<br />
assumptions enables one to be certain that assumptions are valid<br />
and realistic. Verification can be done through market research.<br />
Running a start-up without market research as a key<br />
component in the business plan is like travelling down a highway<br />
with a blindfold on; Market research for start-ups is essential<br />
as the organization is at a sensitive stage in understanding the<br />
needs of their target market. Understanding one’s target market<br />
can be a benchmark in evaluating the success of a start-up and<br />
also to help start-ups validate their assumptions. Market research<br />
will guide entrepreneurs in making strategic business decisions,<br />
uncovering unmet customer needs, and in many cases, help to<br />
discover new ideas for products or services.<br />
Infographic continued from Page 7<br />
Next Issue: March 15, 20<strong>13</strong><br />
Want to contribute? Got a story?<br />
Send email to:<br />
editor@pctechmagazine.com<br />
De<strong>ad</strong>line: Friday March 10, 20<strong>13</strong><br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
SPECIAL 23
FEATURES<br />
24<br />
REPORTS, ANALYSIS<br />
10 things the comments section...<br />
...taught me<br />
about the Web<br />
AS WE<br />
HIT THE<br />
ROAD FOR<br />
ANOTHER<br />
YEAR,<br />
the pace<br />
of business<br />
may slow<br />
momentarily,<br />
making it a good<br />
time to take stock<br />
of your startup’s IT<br />
assets, spending and<br />
future plans. Inevitably, someone –<br />
maybe the chief financial officer, maybe an<br />
investor – will want to know how much the company<br />
spent on technology over the past year. In <strong>ad</strong>dition,<br />
there are tasks to complete now, in order to start fresh<br />
in the new year.<br />
Of all the challenges faced by those who put content<br />
online, the comments facility must be the most vexing<br />
one. (There’s even a Twitter account, @AvoidComments,<br />
which reminds followers not to re<strong>ad</strong> the comments,<br />
ever. Sample tweet: Whenever you see a smiling child,<br />
remember: she’s never re<strong>ad</strong> a comment in her life, and<br />
she’s doing just fine.)<br />
Many websites have experimented with reining in<br />
the b<strong>ad</strong> behaviour that predominates in a facility that<br />
offers a toxic combination of visibility and anonymity.<br />
Imposing standards all too often means sacrificing<br />
interaction, however. Recently, TechCrunch announced<br />
that it’s bringing its comments facility back; channelling<br />
comments via Facebook resulted in a precipitous dropoff<br />
in engagement, so now it’s trying LiveFyre.<br />
I usually don’t re<strong>ad</strong> the comments on one of the<br />
platforms I blog on, and haven’t for years. This is s<strong>ad</strong>,<br />
because I’ve always thought of blogging, unlike the<br />
opinion pieces or features I write, as a fundamentally<br />
social act. You write in the expectation that others<br />
will have a view on what you’ve written, and the text<br />
is created in the space between your post and the<br />
reactions to it.<br />
If I stopped re<strong>ad</strong>ing the comments, it’s because they<br />
became a strain on my sanity. To survive them, writers<br />
need<br />
to have<br />
thick skin, or<br />
be a masochist, or<br />
both, and I know of bloggers<br />
who stopped writing because they<br />
couldn’t handle the vitriol. Actually, I don’t<br />
know of anyone who can spend any time re<strong>ad</strong>ing the<br />
comments on some websites without wanting to stab<br />
themselves in the eye with a hot fork. But trolling and<br />
abusive comments are par for the course, so much<br />
so that serious research has been conducted into why<br />
people behave so b<strong>ad</strong>ly online.<br />
Researchers have found that that people online<br />
have lower levels of self control. (Oh yes, and spending<br />
too much time on Facebook makes you fat – the more<br />
people spent online, the more likely they were to<br />
engage in binge eating).<br />
In my years of blogging, I’ve learned a thing or two<br />
from the comments facility.<br />
1. There’s a kind of Kevin Bacon game going on<br />
In the Kevin Bacon game so popular in the 1990s, the<br />
challenge was to link any actor to Kevin Bacon. In the<br />
comments facility, the challenge is to see how long it will<br />
take for the comments on any post to devolve into a<br />
slanging match between – for want of a better term —<br />
liberals and conservatives.<br />
Take this report (http://www.independent.co.uk/<br />
news/world/americas/bound-beaten-and-robbedbackpackers-attacked-by-whipbrandishing-peruvianvillagers-in-savage-two-day-ordeal-8480069.html)<br />
from a UK news website on a group of American tourists<br />
attacked in Peru.<br />
The first comment takes a swipe at liberals and it<br />
goes downhill from there, becoming nothing more than<br />
an opportunity for Republicans to fling insults against<br />
Democrats, and vice versa. In South Africa, for<br />
example, all comments facilities ever somehow<br />
end up hosting rants against the ANC and/<br />
or apartheid and/or white privilege, whether<br />
or not the original post h<strong>ad</strong> anything to do<br />
with it. The situation is similar in countries with<br />
similarly torrid pasts.<br />
Which is why….<br />
2. If you want lots of comments, write<br />
about race and/or politics<br />
Around the world, hot button issues range<br />
from gun control to rape. Nothing fires up the<br />
comments facility like discussions about race.<br />
With over 88 000 views and 575 comments,<br />
this post generated far more interaction on<br />
blogging platform Thought Le<strong>ad</strong>er than any<br />
other in the history of the site. The recent FNB<br />
<strong>ad</strong> debacle effectively turned South Africa into<br />
a giant comments facility, with much ranting<br />
about the ANC on various news sites.<br />
Don’t write about race or politics unless you<br />
are very thick skinned or utterly convinced of<br />
the correctness of your views (I’ve learned the<br />
hard way).<br />
3. Abuse is nothing new<br />
The comments facility has just m<strong>ad</strong>e it easier<br />
for people who’d otherwise just rant around<br />
the dinner table, to articulate them in public.<br />
Back in 2004, re<strong>ad</strong>ers were forced to fax<br />
hatemail to the publisher of my satirical pieces<br />
about bitter expats; now all they need to do<br />
is post a comment. Fortunately, the comment<br />
sections on many sites are moderated so<br />
the abusive, <strong>ad</strong> hominem attacks on their<br />
bloggers are mostly filtered out. If I got to<br />
see the comments they didn’t let through, my<br />
insomnia would probably be worse than it<br />
alre<strong>ad</strong>y is.<br />
4. We’re talking a small number of<br />
people<br />
Editor of News24 (a division of emerging<br />
markets media giant Naspers) Jannie<br />
Momberg says about one percent of re<strong>ad</strong>ers<br />
comment, and of those, around 10% are<br />
abusive. “News24 comments” remains<br />
a byword for aggressively stupid, racist<br />
comments, but that’s not really fair because<br />
the same behaviour can be seen in the<br />
comments facilities of other news websites,<br />
too. In fact, the comments on a couple of<br />
recent pieces have been sane and reasonable<br />
for the most part.<br />
5. The same names crop up everywhere<br />
Spend any time re<strong>ad</strong>ing news or comment<br />
and you’ll spot the same familiar names and<br />
pseudonyms, banging the same drum they’ve<br />
been beating for years. Commenting must<br />
virtually be a full time job for some of them,<br />
and they never seem to get bored.<br />
6. Very few people actually re<strong>ad</strong> what<br />
they comment on<br />
This is what really grates me. If I go to the<br />
trouble of putting together an argument, the<br />
least I expect is for the re<strong>ad</strong>er to take in what<br />
I’ve actually written before commenting. S<strong>ad</strong>ly,<br />
the typical re<strong>ad</strong>er strategy seems to be: re<strong>ad</strong><br />
the he<strong>ad</strong>ing, scan through the body of the<br />
text, blurt out the first thing that comes to<br />
mind.<br />
Most popular columnists and bloggers have<br />
regular re<strong>ad</strong>ers who know them well, or think<br />
they know them well, so by the time the latter<br />
click on the link, they’ve alre<strong>ad</strong>y m<strong>ad</strong>e up their<br />
minds (familiarity, alas, breeds contempt — on<br />
both sides). They re<strong>ad</strong> what they think they<br />
see, then argue with their own projections.<br />
Much of the so-called debate in the comments<br />
facility is a form of ideological sh<strong>ad</strong>ow-boxing.<br />
7. Angry, abusive comments beget more<br />
angry, abusive comments<br />
Take any divisive topic – in this case, climate<br />
change. According to this study, the more<br />
abuse in the comments facility, the more<br />
it will inflame others who might otherwise<br />
have been reasonable. Study co-author<br />
Dietram Scheufele, a professor of science<br />
communication at the University of Wisconsin-<br />
M<strong>ad</strong>ison, pointed out that the comments<br />
m<strong>ad</strong>e what used to be a private act now more<br />
like “re<strong>ad</strong>ing the news article in the middle of<br />
the town square, with people screaming in my<br />
ear what I should believe about it.”<br />
8. There will be mansplaining<br />
Mansplaining is the practice of men telling<br />
women what she’s actually thinking because,<br />
poor thing, she’s misinformed. Because<br />
commenters don’t list their gender, it’s<br />
impossible to make a reliable assessment of<br />
whether men comment more than women,<br />
but my impression is that they do. Any female<br />
blogger who writes on a platform where<br />
there are many male re<strong>ad</strong>ers knows all about<br />
mansplaining.<br />
9. The real discussions often happen<br />
elsewhere.<br />
This is something that happened when<br />
TechCrunch shifted to a Facebook-based<br />
comment system. I’ve long held the view that if<br />
people really wanted to debate with bloggers<br />
in a civil manner, they can do it on Twitter or<br />
Facebook. Luckily, I haven’t h<strong>ad</strong> to deal with<br />
much trolling on either platform, and because<br />
there’s more immediacy — the blogger is<br />
there in person, not a disembodied name<br />
attached to words – it’s harder to be abusive.<br />
10. And yes, sometimes the comments<br />
are more interesting than the piece that<br />
inspired them<br />
Sometimes, the comments facility works as it<br />
should, bringing out viewpoints that actually<br />
<strong>ad</strong>d to an understanding of an issue. The<br />
comments on this post on a rather obscure<br />
subject are easier to re<strong>ad</strong> than the piece that<br />
triggered them.<br />
There are no <strong>ad</strong> hominem attacks, and each<br />
commenter seems to be genuinely interested<br />
in teasing apart a complex issue. But this is all<br />
too rare, and probably only happens when<br />
the vast majority of potential commenters are<br />
filtered out by the complexity of an issue.<br />
Recently, I changed my blogging strategy,<br />
writing slightly less contentious material that’s<br />
as much about seeing what responses I get<br />
as it is about putting my opinion out into the<br />
world. A meta post, if you like. As a result, I’ve<br />
started re<strong>ad</strong>ing the comments again — but I’ll<br />
probably stop, because it’s still too depressing:<br />
the same crowd are still saying the same things<br />
they did five years ago. Not that it matters,<br />
really.<br />
The commenters don’t really need me to<br />
participate, because once the post is up, it’s<br />
not mine anymore, but theirs. It takes on a life<br />
of its own, and I am happy to let it go.<br />
Here’s the ultimate irony: if the comments<br />
facility teaches you anything, it’s that if you’re<br />
going to be a writer, and put yourself at the<br />
mercy of others online, you have to learn<br />
to filter out most your re<strong>ad</strong>ers or you’ll stop<br />
writing altogether. As that Twitter account<br />
reminds us: “The next time you’re thinking of<br />
re<strong>ad</strong>ing the comments, do a Google image<br />
search for ‘fluffy puppies’ inste<strong>ad</strong>.”<br />
Have you checked out...<br />
www.directory.pctechmag.com?<br />
— Written by Sarah Britten and first<br />
published by Memeburn.com<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
FEATURES 25
FEATURES<br />
26<br />
USEFUL WEBSITES<br />
Market Analysis:<br />
Mobile Payments In Emerging Nations<br />
Pankaj Kumar is the<br />
chief marketing<br />
officer at F1Soft<br />
International<br />
and specializes<br />
in Strategic<br />
Partnership,<br />
International<br />
marketing,<br />
Global Business<br />
management and<br />
mobile Payments.<br />
He contributes to<br />
Pc Tech’s mobile<br />
Payments section.<br />
Follow Pankaj on<br />
Twitter:<br />
@kumarpankaj1985<br />
BEING A MOBILE PAYMENT PROFESSIONAL, I HAVE always<br />
been curious to identify the elements influencing mobile<br />
commerce business in emerging nations. The growing<br />
ubiquity of mobile phone users proves the potential<br />
of mobile money & extension of services to unbanked<br />
population. Above all, most of the financial institutions,<br />
telcos, vendors are also endorsing mobile payments,<br />
however, the challenges are inevitable. In the recent news,<br />
International Finance Corporation, a member of World<br />
Bank Group is supporting Nepal to develop an efficient<br />
national payment system to regulate all electronic payment<br />
mechanism in the country. This should be a great initiative<br />
to develop the infrastructure in the country in order to<br />
promote mobile money, nevertheless, there are other<br />
segments as well where we should emphasis on.<br />
In spite of last few years of chaos in Nepal, competition<br />
among the financial institutions, money remittances hubs<br />
and telcos has proliferated. There are evidences of financial<br />
institutions actively serving the populations in remote areas<br />
for money remittances while telcos are engaged to expand<br />
the telecommunication spectrum to serve every corner<br />
of nation. Integration of telecommunication system with<br />
financial institutions will be surely urging a revolutionary<br />
changes to the tr<strong>ad</strong>itional banking in remote areas. As of<br />
now, mobile phone users practice sending air time transfer<br />
to another phone, similarly a basic phone can also be<br />
used to manage financial arrangements. As a progression,<br />
very soon we will be using our air time for shopping. The<br />
gigantic volume of remittance has also been the major<br />
factor to induce the technological <strong>ad</strong>vancement in the<br />
region.<br />
In any region across the world, the business model<br />
for mobile money could be Bank driven, Telco driven or<br />
Parternship Led. The regulatory frameworks and AML<br />
compliance need to be well taken care of before jumping<br />
into this space, which eventually strectes a barrier to any<br />
privately held company to start mobile money remittances.<br />
However, if a new entrant follow a partnership led model<br />
with a le<strong>ad</strong>ing bank or telco they can easily spre<strong>ad</strong> to mass<br />
and thereby truncate the market size. Considering two<br />
or three players in the mobile payments space serving a<br />
small region, It becomes mandatory to share merchant<br />
and payout agents. It justifies that even if the consumers<br />
are reluctant to use the mobile money, the threat of new<br />
entrants exist.<br />
Currently the mobile phone is primarily used for voice<br />
or data but taking it to next level in under developed<br />
countries has been a challenge. There are money<br />
remittance hub serving unbanked economies in remote<br />
areas through payout agents thus discouraging the people<br />
to use their mobile phone as a wallet. As long as these big<br />
players are providing substitutes to the services, people will<br />
stick to the tr<strong>ad</strong>itional approach.<br />
Statistics reveals that, Nepal and Bangl<strong>ad</strong>esh come<br />
in the top 5 countries to receive remittances, however<br />
a proficient channel of remittance is still absent in the<br />
region. The investment cost to build a seamless receiving<br />
end for this remittance volume also introduces barrier to<br />
the development. The experience has also claimed that<br />
it’s challenging to any one entity to fulfill all of buyer of<br />
remittances services.<br />
We comprehend that all the risk involved in retail<br />
payments will exist in mobile space as well. However,<br />
winning the confidence of customers should be the priority<br />
on top. In spite of several fraud cases exist in credit card<br />
payment, financial institutions succeeded to obtain the<br />
assurance of consumers. In the same way, we can create<br />
a trusting relationship and convince them to encourage<br />
mobile payments in the nation.<br />
As a conclusion, I would say that we have impressions<br />
of live case studies of mobile payments in developed<br />
countries and we completely understand the future<br />
and benefits of mobile payments. However, educating<br />
user about m-commerce, unified receiving channel<br />
for remittance, existing tr<strong>ad</strong>itional way of banking and<br />
securities should be <strong>ad</strong>dressed on priority basis, otherwise<br />
the vision of mobile money will only be fragmentary.<br />
Reviews?<br />
Checkout... and make an informed decision before<br />
you buy next time!<br />
www.reviews.pctechmag.com<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
FEATURES <strong>27</strong>
FEATURES<br />
28<br />
The Dark SiDe of<br />
Computers<br />
Technology may have enriched all our lives, but it has also been used for<br />
nefarious purposes by unscrupulous governments, criminals and terrorists. In<br />
this feature, we try to explain how computers have helped to perpetrate evil<br />
around the world.<br />
During the six dec<strong>ad</strong>es or so that<br />
they’ve been around, computers<br />
have brought dramatic changes to<br />
our understanding of the world and<br />
the ways in which we work and communicate.<br />
The technology has generated our homes,<br />
cars and pockets, driving changes in our<br />
culture, behavior and governance.<br />
Most of this change has been for the good:<br />
we now communicate more easily, can work<br />
more efficiently and are better entertained<br />
than ever before. However, the foundations of<br />
today’s technology were built amid the darker<br />
motives and necessities of the Second World<br />
War and the Cold War that followed, and<br />
the history of computing contains troubling<br />
examples of the pursuit of power and profit at<br />
the expense of people’s lives.<br />
Computers have been used for evil<br />
deeds, and through bugs or negligence have<br />
accidentally committed dre<strong>ad</strong>ful acts, but the<br />
ongoing development of artificial intelligence<br />
and autonomous systems raises an even<br />
more frightening prospect. Could ever more<br />
intelligent computers be used for ever greater<br />
evil, or could they leap above the humanity<br />
that created them and, living up to the darkest<br />
imaginings of science fiction, themselves<br />
become evil?<br />
Could technological evolution reach a<br />
tipping point beyond which humans, when it<br />
comes to survival, are no longer ‘the fittest’?<br />
GOING BALLISTIC<br />
Computer-based technologies such as GPS<br />
and digital X-rays help to protect and save<br />
lives everyday, but modern computers are<br />
built upon <strong>ad</strong>vances undertaken in darker<br />
times. The origins of computing were<br />
innocent enough, with some of the earliest<br />
programmable machines developed by<br />
Joseph Marie Jacquard to automate looms<br />
in the textile industry in the 1800s. The first<br />
theoretical computer, Charles Babbage’s<br />
‘analytical engine’, was originally devised<br />
simply to remove human errors from the<br />
mathematical tables available in the early 19th<br />
century.<br />
The motivations for these inventions may<br />
have been innocent, but the computer as<br />
we understand it today wasn’t fully imagined<br />
until the years le<strong>ad</strong>ing up to World War II,<br />
and it was the war that provided the money,<br />
facilities and impetus for the theories of<br />
computer scientists such as Alan Turing<br />
to be m<strong>ad</strong>e real. It was the need among<br />
the analysts at Bletchley Park for massive<br />
computing power that drove development,<br />
first of the electromechanical ‘Bombe’ and<br />
‘Heath Robinson’ machines and subsequently<br />
of Colossus – the first programmable, digital,<br />
electronic computer.<br />
Being the product of a war effort doesn’t<br />
automatically render a computer ‘evil’,<br />
of course. The Colossus computers were<br />
famously used to mount ‘brute force’ attacks<br />
on the Lorenz cipher used by the German<br />
High Command, work that helped to save<br />
Allied lives and almost certainly shortened<br />
the duration of the war in Europe, even if Axis<br />
soldiers, and inevitably civilians, were killed in<br />
actions taken on the basis of the intelligence.<br />
Things are muddier, though, for other war-era<br />
computers, such as ENIAC.<br />
ENIAC, a huge electronic ‘brain’ weighing<br />
more than <strong>27</strong> tonnes and containing<br />
more than 17,000 thermionic valves, was<br />
commissioned and funded by the United<br />
States Army and developed in secret at<br />
the University of Pennsylvania from 1943.<br />
Operational from 1946 until 1955, ENIAC was<br />
a ballistics computer, designed specifically to<br />
calculate artillery firing tables.<br />
The very reason for its existence was to<br />
improve the accuracy and de<strong>ad</strong>liness of<br />
the army’s firepower, but while still under<br />
development it came to the attention of the<br />
mathematician John von Neumann, then<br />
working in the Manhattan Project on the<br />
development of the hydrogen bomb. The<br />
computer’s first test run was computations for<br />
the bomb. It’s hard to say whether ENIAC was<br />
instrumental, but the lethality of mankind’s<br />
arsenal has certainly been improved thanks to<br />
computers.<br />
DARK HISTORY<br />
While the building of weapons (nuclear<br />
or otherwise) is a divisive debate, often<br />
dependent on who and why they are<br />
deployed, other examples of computer use<br />
seem harder to defend. In the 2001 book IBM<br />
and the Holocaust, US journalist Edwin Black<br />
alleges that IBM and its German subsidiary<br />
Dehomag developed and continued business<br />
relationships with the Nazi regime from Hitler’s<br />
1933 rise to power until the 1945 downfall of<br />
the Third Reich.<br />
In particular, Black looks at the role of<br />
Hollerith punchcard machines, supplied<br />
by Dehomag, in the identification and<br />
cataloguing of Jews in the 1930s, and of IBM<br />
technology in the organisation of railro<strong>ad</strong>s<br />
and registration at concentration camps. His<br />
book alleges that IBM’s subsidiaries leased,<br />
rather than sold, equipment to the Third<br />
Reich, that they maintained and upgr<strong>ad</strong>ed<br />
punchcard machines throughout the war, and<br />
that Dehomag trained Nazi officers including<br />
concentration camp <strong>ad</strong>ministrators.<br />
The full extent of IBM’s involvement with<br />
the Third Reich is disputed, but Dehomag,<br />
which h<strong>ad</strong> come under the control of Nazi<br />
authorities, did provide Hollerith equipment<br />
that was used for census operations vital to<br />
the Third Reich as it pursued various actions<br />
against its own citizens and those of annexed<br />
and inv<strong>ad</strong>ed countries. Although the systems,<br />
designed to log data re<strong>ad</strong> from punchcards,<br />
weren’t strictly computers, they were close<br />
cousins, and there’s no doubt they helped to<br />
make terrible acts possible.<br />
COMPUTER PARTITION<br />
While the crimes of the Nazis might stand<br />
alone in their brutality, history offers other<br />
examples of regimes who used computers<br />
for unsavoury purposes. The South African<br />
government m<strong>ad</strong>e extensive use of computers<br />
under apartheid to keep track of its citizens<br />
and help enforce the division between racial<br />
groups.<br />
An arms embargo was enforced upon<br />
South Africa from 1977, but computers<br />
were still sold for years after. In 1980 a UN<br />
Committee told the Security Council that the<br />
export of computers should be prohibited. In<br />
1985 and 1986 the Security Council and EU<br />
both halted exports of computers for police or<br />
military use.<br />
However, a total embargo wasn’t enforced,<br />
so the ruling h<strong>ad</strong> little effect on government<br />
procurement of computers.<br />
Although it’s hard to link computers directly<br />
to acts of violence against citizens, computers<br />
were certainly used to control their movement<br />
and restrict their human rights. Black citizens<br />
were each given passbooks detailing where<br />
they could go, live and work, and these were<br />
tied into a computerized population register<br />
for easy reference.<br />
A further possible example is Iraq under<br />
S<strong>ad</strong>dam Hussein which, according to an<br />
unsubstantiated December 2000 story on the<br />
conservative World Net Daily website, once<br />
sought to build a supercomputer from 4,000<br />
Sony PlayStation 2 consoles. Quotes attributed<br />
in the article to a ‘military intelligence officer<br />
who declined to be identified’ re<strong>ad</strong> more like<br />
the exaggerations of a PlayStation marketer,<br />
however, focusing on ‘staggering’ graphics<br />
capabilities that were “roughly 15 times more<br />
powerful than the graphics cards found in<br />
most PCs”.<br />
Despite the story’s dubious feel, it is likely<br />
that S<strong>ad</strong>dam’s regime would have been more<br />
dangerous were it not for the embargo on<br />
buying more conventional computing power.<br />
It’s certainly true that today, consumer<br />
PCs with multicore processors and massively<br />
parallel graphics processors can be combined<br />
in distributed computing projects such as<br />
Folding@home to tackle the most complex<br />
of problems. The world’s most powerful<br />
computer, the Cray Titan based in Oak Ridge,<br />
Tennessee, owes its supremacy to a 2012<br />
upgr<strong>ad</strong>e that, among other things, installed<br />
18,688 Nvidia Tesla K20 GPUs.<br />
EVERYDAY EVILS<br />
While supercomputers (of whatever era) are<br />
often used for sh<strong>ad</strong>owy purposes, anyone’s PC<br />
could be co-opted to act maliciously.<br />
There are many examples of malware that<br />
turn computers into a botnet; a group of<br />
distributed computers under the control of a<br />
hacker, activist or sometimes even the agents<br />
of a state. While botnets don’t usually offer<br />
much computing power, a large botnet can<br />
flood a website or online service with data<br />
requests, overwhelming its ability to respond<br />
and temporarily preventing the service’s<br />
legitimate use – a tactic known as a distributed<br />
denial-of-service (DDoS) attack.<br />
While many such attacks are certainly<br />
criminal or malicious, some highly targeted<br />
examples might be considered ‘evil’. In the<br />
South Korean by-elections of April 2011, for<br />
example, DDoS attacks targeted the websites<br />
of the National Election Commission and of<br />
mayoral candidate Park Won-soon, making<br />
it harder for the electorate to look up details<br />
of where and when to vote and, potentially,<br />
influencing the turnout and outcome of the<br />
election. Police later arrested the secretary of<br />
the Grand National Party and four others in<br />
association with the attacks.<br />
In recent times, the comparative ease with<br />
which a DDoS attack can be mounted has<br />
helped it to become a tool with which activists<br />
can attack the institutions with which they<br />
disagree, whether the targets be commercial<br />
or political. One example is the ongoing DDoS,<br />
hacking and other attacks by pro-Israeli and<br />
pro-Palestinian groups that, at the beginning<br />
of 2012, resulted in the downing of the Tel<br />
Aviv stock exchange, First International Bank of<br />
Israel and Israeli national carrier El Al websites,<br />
followed by the retaliatory taking down of the<br />
Saudi and UAE stock exchange websites.<br />
Such attacks are deliberate, but a website<br />
can be overwhelmed by genuine demand, and<br />
a service can be swamped as a result of a bug<br />
in internet hardware such as a router.<br />
Such bugs, or simple mistakes, can<br />
quite often be the root cause of computer<br />
behaviour that, to the casual observer, might<br />
seem malicious. As an example, a simple data<br />
entry mistake could result in a black mark on<br />
a customer’s credit score that subsequently<br />
prevents them obtaining another service for<br />
which they should in fact be eligible.<br />
Such mistakes are routinely m<strong>ad</strong>e, but may<br />
not be so easy to correct. In November 2012,<br />
the financial services company Prudential<br />
was fined £50,000 by the Information<br />
Commissioner’s Office (ICO) in a case where<br />
the records of two customers h<strong>ad</strong> been<br />
mistakenly merged. The mistake, originally<br />
m<strong>ad</strong>e by one of the customer’s financial<br />
<strong>ad</strong>visors, was understandable as the two<br />
customers shared the same forename,<br />
surname and date of birth, but the fine arose<br />
because Prudential failed to investigate<br />
properly when told of the problem.<br />
In every area where modern technology<br />
gathers, stores and shares information about<br />
us there’s the potential for such mistakes,<br />
but there’s also the potential for deliberate<br />
exploitation. In Google’s early years – a<br />
company whose entire reason for being is to<br />
‘organise the world’s information’ – its staff<br />
recognised this threat, <strong>ad</strong>opting the informal<br />
motto ‘Don’t be evil’. It’s still referenced<br />
prominently in the company’s code of conduct,<br />
although critics might question the extent to<br />
which it influences behaviour.<br />
Companies aren’t the only organisations<br />
that gather data, with governments across the<br />
world eager to retain their grasp on citizens’<br />
communications and activities as they use new<br />
tools such as social networks.<br />
In the worst cases, technology delivers new<br />
tools for potential oppression and suppression,<br />
from facial or number-plate recognition and<br />
tracking in CCTV networks, to censorship or<br />
blocking of the web and other services.<br />
WAR MACHINES<br />
There’s a limit to the damage that can be<br />
done through the gathering and analysis of<br />
information or by simple mistakes, but the<br />
same isn’t true of computer systems that<br />
are designed to act on sh<strong>ad</strong>owy information<br />
or to do harm in the first place. Weapons<br />
technology didn’t stop with the development<br />
of the first ballistic computers; modern warfare<br />
relies on a plethora of computerized systems<br />
that help map the battlefield, locate and<br />
identify friendly troops and enemy targets and,<br />
ideally, destroy only the latter.<br />
Some, such as GPS, indubitably have<br />
far-reaching and peaceful applications, while<br />
others such as missile guidance systems may<br />
be more specialised.<br />
We often hear of ‘pinpoint’, ‘surgical’ or<br />
‘targeted’ strikes in the context of military<br />
action, but even the most accurate decisions<br />
and infallible targeting are only as good as the<br />
information on which they’re based.<br />
When the US declared war on Iraq in March<br />
2003, it launched a cruise missile strike against<br />
a supposed le<strong>ad</strong>ership bunker and other<br />
targets in the hope of wiping out S<strong>ad</strong>dam<br />
Hussein and his command, yet the objectives<br />
weren’t met. Iraqi sources claimed that nonmilitary<br />
targets h<strong>ad</strong> been hit and civilians<br />
wounded, while CBS later reported that the<br />
bunker h<strong>ad</strong> never existed.<br />
In the past dec<strong>ad</strong>e or so, the US in<br />
particular has intensified its use of unmanned<br />
aerial vehicles (UAVs), colloquially referred to<br />
as drones, for surveillance and air strikes, both<br />
within theatres of war such as Afghanistan, and<br />
outside such as in Pakistan.<br />
Drones are appealing to security agencies<br />
and the military because they’re cheaper<br />
than an aeroplane, and can be deployed in<br />
dangerous or illegal missions without risking<br />
a pilot’s life, or the difficulties should they be<br />
shot down and held captive. However, by<br />
reducing human involvement in the gathering<br />
of intelligence data and offensive missions that<br />
rely on it, many argue that unmanned vehicles<br />
increase the risk that innocent people will be<br />
killed.<br />
It’s often difficult to verify casualty reports<br />
from regions in which drones are used<br />
offensively, but there are numerous reports of<br />
civilians being caught up in supposedly highly<br />
targeted strikes. Among the 3,000 people<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
FEATURES 29
FEATURES<br />
30<br />
estimated by the Bureau of Investigative<br />
Journalism to have lost their lives since 2004<br />
in drone strikes within Pakistan, it’s reported<br />
that civilian casualties number between<br />
473 and 889. Other estimates are far more<br />
pessimistic. Writing for the Washington-based<br />
Brookings think tank in July 2009, Middle East<br />
security expert Daniel L Byman estimated that<br />
for every militant killed by drone strikes, 10<br />
civilians might also lose their lives.<br />
NAUGHTY BY NATURE?<br />
Whatever the exact figures, it’s debatable<br />
whether weapons of war are inherently evil<br />
while they’re under the control of humans,<br />
who bear the moral and legal responsibility<br />
for their use. However, drone technology has<br />
improved, and the US Air Force believes that<br />
“<strong>ad</strong>vances in artificial intelligence (AI)… will<br />
enable systems to make combat decisions and<br />
act within legal and policy constraints without<br />
necessarily requiring human input”.<br />
In other words, a future generation of<br />
drones might decide for itself who to kill.<br />
There’s clearly great risk in such a situation.<br />
“Military robots are potentially indiscriminate,”<br />
cautions Patrick Lin, a Stanford University<br />
researcher quoted by US news website<br />
the Global Post. “They have a difficult time<br />
identifying people as well as contexts; for<br />
instance, whether a group of people are<br />
at a political rally or wedding celebration.”<br />
Weapons and AI researchers caution that there<br />
is no plan for humans to be totally removed<br />
from the process, but the military currently<br />
doesn’t have enough trained operators<br />
to meet the demand for UAV sorties, so<br />
increased automation would certainly be a<br />
great benefit.<br />
While fully autonomous drones might<br />
be considered evil – especially if in practice<br />
they prove to be less discriminate than<br />
human-piloted weapons – in reality even<br />
these weapons can’t truly be evil without the<br />
intelligence, consciousness and morals of a<br />
human being. In all of the examples we’ve<br />
looked at so far, where evil has been done it’s<br />
come from those who designed or used the<br />
technology rather than the technology itself,<br />
but with computers increasingly able to ‘think’<br />
for themselves, will this always be the case?<br />
Artificial intelligence is still a distance away<br />
from the super-intelligent systems envisaged<br />
by computer scientists and writers, but these<br />
may still be closer than we’d think. Computer<br />
brains may not be able to tackle the reasoning,<br />
thought, <strong>ad</strong>aptability and self-learning of the<br />
human mind, but for some time they’ve been<br />
able to beat humans at highly specific tasks,<br />
such as preventing a car’s wheels locking<br />
during hard braking or playing chess. More<br />
recently the best artificial systems have begun<br />
to outperform humans at more complex<br />
tasks such as facial recognition, and progress<br />
continues.<br />
GHOST IN THE MACHINE<br />
While it’s uncertain whether we’ll ever succeed<br />
in modelling the exact nature of the human<br />
brain, it’s highly likely that we will manage<br />
to create a machine with a similar level of<br />
intelligence and, ultimately, a computer<br />
that’s substantially more intelligent than us.<br />
This event is the basis for the concept of<br />
‘singularity’ in the field of artificial intelligence;<br />
a scenario in which mankind creates an<br />
intelligent machine that’s more capable than<br />
we are of designing subsequent intelligent<br />
machines. These in turn will create computers<br />
that are an order of magnitude more clever,<br />
and so on, le<strong>ad</strong>ing to a sudden and –<br />
potentially – unlimited explosion in the intellect<br />
and utility of computers.<br />
Such a scenario raises some astonishing<br />
possibilities. With unlimited intelligence, future<br />
computers could be used to solve problems<br />
that have so far defeated humans, such as<br />
curing disease, inventing a safe and limitless<br />
power source or theorising a new physical<br />
model for the universe that incorporates<br />
particles, gravity and all the other observed<br />
phenomena. They could even tackle vexing<br />
philosophical problems such as the existence<br />
or otherwise of God, or the meaning of life<br />
itself – a scenario anticipated by Douglas<br />
Adams in The Hitchhiker’s Guide to the <strong>Galaxy</strong>,<br />
where the computer Deep Thought designs<br />
Earth, the computer, to devise the ultimate<br />
question.<br />
A more earthly concern is that, while the<br />
tipping point for an AI singularity doesn’t<br />
require an artificial intelligence similar to<br />
our own, it’s quite probable that something<br />
similar will arise at some point after singularity<br />
is reached. This raises the possibility that<br />
computers could come to ‘think’ or be<br />
conscious in a similar sense to us, and to<br />
understand morality and the concepts of good<br />
or evil for the first time.<br />
Philosophically, the actions of computers<br />
with such an understanding could, finally, truly<br />
be said to be good or evil.<br />
It’s an intriguing concept, disquieting for<br />
some, but even more thorny is the thought<br />
that a machine morality borne of a different<br />
intelligence and consciousness to ours is likely<br />
not only to have different interests, but to have<br />
a different concept of morality.<br />
In other words, a computer with nothing<br />
but good intentions could prove incredibly<br />
evil by our standards, because its interests,<br />
morality and thus its understanding of evil<br />
wouldn’t reflect our own.<br />
ABSOLUTE POWER<br />
Asked if there would ever be a computer<br />
as intelligent as humans, US author and<br />
singularity proponent Vernor Vinge replied:<br />
“Yes. But only briefly.” Even in a scenario<br />
where technology remains benign, there exists<br />
the possibility for mankind to lose control of<br />
it and ultimately face competition for energy<br />
and materials from, for want of a better word,<br />
a species of our own creation.<br />
While such an outcome sounds far-fetched,<br />
it’s realistic enough that it’s now coming to<br />
be considered quite seriously. In November<br />
2012, such concerns led to the formation at<br />
the University of Cambridge of the Centre for<br />
the Study of Existential Risk (CSER), specifically<br />
to consider ‘extinction-level’ risks posed to<br />
humans by their own technology.<br />
Writing jointly on the Australian ac<strong>ad</strong>emic<br />
website The Conversation, CSER founders Jaan<br />
Tallinn and Huw Price likened the prospect of<br />
uncontained singularity to a ticking bomb. On<br />
containing the risk, they wrote: “A good first<br />
step… would be to stop treating intelligent<br />
machines as the stuff of science fiction, and<br />
start thinking of them as a part of the reality<br />
that we or our descendants may actually<br />
confront, sooner or later. Once we put such<br />
a future on the agenda we can begin some<br />
serious research about ways to ensure<br />
outsourcing intelligence to machines would be<br />
safe and beneficial, from our point of view.”<br />
Some ac<strong>ad</strong>emics have suggested that a<br />
potential strategy by which we could achieve<br />
this is to create only human-based AI, which<br />
will share our human values and thus be<br />
likely to share and protect our interests. A key<br />
problem here is that it seems unlikely that<br />
the first super-intelligent AI we create will be<br />
similar to ours, and it’s by no means certain<br />
that we’ll ever duplicate the exact nature of the<br />
human brain.<br />
An alternative argument espoused by Tallinn<br />
and others is to limit artificial intelligences to<br />
narrow domains, such that AI can never reach<br />
the generalised superintelligence that would in<br />
all likelihood be necessary to displace humans.<br />
Certainly, this approach appears more feasible<br />
against the background of our current<br />
progress, which has delivered super-human<br />
ability only in very narrow applications.<br />
TOOLS OF THE TRADE<br />
Computers are probably mankind’s greatest<br />
tools and, like other tools, the purposes for<br />
which we wield them can be good, neutral or<br />
evil. They usually do our bidding, and where<br />
they don’t it’s usually by an accident of our<br />
design. Either way, the moral responsibility<br />
is with us. The future promises increased<br />
intelligence and autonomy, however, and<br />
the prospect that computers may evolve<br />
beyond our control. In such a scenario artificial<br />
intelligence may act according to its own<br />
morality. If we fail to ensure that this is aligned<br />
with ours, we may deliberately or otherwise<br />
unleash the first truly evil computers.<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
FEATURES 31
FEATURES<br />
32<br />
Buying aeroplane tickets, buying<br />
domain names, the odd concert ticket, movie<br />
ticket and books online is pretty much where<br />
most of us feel comfortable when we talk<br />
ecommerce. We generally like to touch and<br />
feel things when we are looking at buying<br />
tangible goods. But while we have been<br />
looking and touching; the rest of the world has<br />
taken to ecommerce like a humpback whale<br />
to krill.<br />
A recently released eMarketer report<br />
estimates that Business 2 Consumer (B2C)<br />
ecommerce sales rose 21.1% in 2012 to a<br />
stunning one trillion US dollars. This all-time<br />
high figure is predicted to increase a further<br />
18.3% to US$1.298-trillion in 20<strong>13</strong>.<br />
These figures are almost incomprehensible<br />
especially when we compare the regions in the<br />
graph below.<br />
Albert Mucunguzi<br />
Albert is the Founder and CeO of pC Tech Magazine. He contributes to pC<br />
Tech Blogs, and runs another popular blog called “Thinking Different” on<br />
http://almuc.me. You can follow him on Twitter at @albertmuc, or get share<br />
your comments about his articles via the email, albert@pctechgroup.net<br />
Ecommerce Is Now A Trillion Dollar<br />
Industry: Here’s How It Happened<br />
The Asia-Pacific market makes the Middle<br />
East and African markets look like they are<br />
standing still, with the former region holding<br />
30.5% of the market and the later eking out a<br />
paltry 1.9% in 2012.<br />
According to ComScore, 90% of Americans<br />
(about 194-million people) visited retail<br />
shopping sites in December of 2012. That<br />
194-million is part of the reason why the MEA<br />
region is lagging behind. America simply has<br />
a large bulk of connected users. MEA’s total<br />
digital buyers amount to 40.9-million people<br />
in 2012.<br />
Low internet connectivity, poor<br />
infrastructure and a lack of education have<br />
been cited as major reasons as to why<br />
ecommerce particularly is an industry that<br />
developing nations struggle with. So what are<br />
the major draw cards that make people shop<br />
online and not offline in the brick and mortar<br />
stores?<br />
1. CONVENIENCE<br />
Where else can you do shopping at midnight<br />
in your birthday suit? Not at your local corner<br />
shop that’s for sure. Online shops are 24/7<br />
and there are no lines, queues, disgruntled<br />
employees or other irate customers to deal<br />
with.<br />
2. BETTER PRICES<br />
Nine times out of 10 it costs shoppers less<br />
to shop online than in the physical store. It<br />
costs the shop keepers less so they pass this<br />
discount on to their online clients.<br />
3. SEND GIFTS<br />
Online shopping makes it super easy to give<br />
and send gifts to loved ones. The retailers<br />
often offer “gift wrapping” as part of their<br />
service as well as (obviously) delivery. This<br />
takes all of the hassle (and excuse) out of gift<br />
giving to those who might be in another town<br />
or country.<br />
4. COMPARISON OF PRICES<br />
Online shops make comparison and research<br />
of products and prices possible.<br />
5. DISCREET PURCHASES<br />
Sometimes it is better to not be seen whilst<br />
shopping for those, erm, special products that<br />
you would rather not have your pastor see<br />
you buy. Online shopping offers anonymity<br />
when you need it most.<br />
Lock up your mailbox<br />
I’D LIKE TO use this month’s column<br />
to highlight an increasingly prevalent<br />
cybercrime that is causing distress,<br />
concern and, in some cases, real<br />
financial damage: email hacking. In<br />
recent weeks, I have spoken with victims<br />
of email hacks. The real-life testimony of<br />
how their lives were turned upsidedown<br />
and the difficulty involved in recovering<br />
their accounts compelled me to explore<br />
this phenomenon further.<br />
The trouble is that we all hang<br />
on to old emails as a way to store<br />
valuable information such as website logons,<br />
verification emails and financial transaction<br />
details that are kept ‘just in case we need<br />
them’. In some circumstances, this information<br />
can hold the key to your online identity.<br />
Storing it in web-based email accounts is an<br />
invitation to any would-be hacker.<br />
GROUP DYNAMIC<br />
So how are these accounts compromised<br />
in the first place? The most common way<br />
is by phishing or key-logging malware. I’ve<br />
discussed these hacking methods in previous<br />
columns, so I don’t intend to go over them<br />
again. However, there’s another method that’s<br />
becoming increasingly common method:<br />
social engineering. Hackers inveigle their<br />
way into accounts by first accumulating<br />
information on a target. This information is<br />
then used to answer security questions in<br />
order to gain access to the account. I was told<br />
of a hacker who h<strong>ad</strong> gained control of his<br />
victim’s Facebook account by way of an initial<br />
email compromise. This allowed him to send<br />
messages to the victim’s friends, claiming that<br />
he h<strong>ad</strong> lost his phone and needed the mobile<br />
number and email <strong>ad</strong>dress of a particular<br />
person in order to contact him.<br />
Having obtained this information, it<br />
was used to change the specified security<br />
phone number on the second victim’s email<br />
account, so allowing a further email account<br />
compromise to be attempted.<br />
Fortunately, when the first victim logged<br />
on to his Facebook account, he noticed the<br />
phantom conversation and phoned the<br />
compromised friend to alert him, and the<br />
game was up.<br />
To be fair, web-based email providers are<br />
aware of the problem and have taken steps<br />
to increase security. It’s worth knowing how<br />
these steps can help you ‘target harden’ your<br />
particular account.<br />
HAVE A WORD<br />
First and foremost, make sure your passwords<br />
are strong enough. How many of your<br />
passwords for different accounts are identical?<br />
Come on, answer truthfully. When faced with<br />
an online registration form, the temptation to<br />
use the same old password is overwhelming.<br />
One compromised database, though, and<br />
you’ve handed out your keys for all the others.<br />
When was the last time you changed your<br />
email password? Ok, confession time: in my<br />
case, it was two years ago. I discovered this<br />
alarming fact when I opened the control<br />
dashboard of one of my email accounts and,<br />
as a result, I immediately changed it. It’s good<br />
practice to change your email passwords<br />
regularly; it’s painful, I know, but do it, and if<br />
you have been compromised and the b<strong>ad</strong><br />
guys have yet to use these details, they will be<br />
useless to them when the time comes.<br />
Think of a password that’s at least eight<br />
characters long with alphanumeric and<br />
special symbols, then copy and paste it into<br />
a password folder (along with the relevant<br />
website details) and secure that folder on<br />
your machine. Don’t name the folder<br />
‘Passwords’, though, will you?<br />
A recent study of passwords used in<br />
a popular database found that a cracker<br />
with a dictionary of only 5,000 words<br />
could brute-force his way into all the<br />
accounts held on that database.<br />
Brute-forcing is a method of guessing<br />
passwords repeatedly until the correct<br />
one is found, and there are programs<br />
out there that can do this automatically.<br />
To help avoid this, some providers have<br />
a form of twofactor authentication, which<br />
allows a phone number to be linked to the<br />
account so texts are sent directly to you in<br />
the event of a password reset attempt. Go<br />
into your email control panel to see if you can<br />
enable this.<br />
Next, tie your Facebook account down<br />
by restricting who can view your page and<br />
who can see your friends. Facebook is fast<br />
becoming the hacker’s tool of choice for<br />
compromising email accounts and data<br />
gathering, so it makes sense to restrict who<br />
can interact with you. Also, don’t assume that<br />
requests for details that appear to come from<br />
friends are what they seem. If in doubt, call<br />
your friend directly to make sure the request<br />
is genuine.<br />
Finally, clear your inbox of all emails that<br />
could be used against you – the password<br />
confirmation emails, the account detail emails,<br />
the ‘confirmation of transaction’ emails. Copy<br />
them into a secure folder and then delete<br />
them from your inbox. It’s the cyber equivalent<br />
of a clear desk policy.<br />
MAIL PROTECTION<br />
If you look around YouTube, you’ll see a<br />
large group of people who think it’s funny<br />
to compromise email accounts: it’s not. It’s a<br />
criminal offence, and the chances of being<br />
caught and prosecuted are increasing. But<br />
we should all do our bit to make things more<br />
difficult for would-be hackers by beefing up<br />
our email security.<br />
You know it makes sense.<br />
Follow your favourite<br />
blogger every week!<br />
http://blogs.pctechmag.com<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
FEATURES 33
FEATURES<br />
34<br />
Why life through<br />
Google Glass...<br />
It’s hard to engineer this kind of creepy<br />
serendipity. Earlier this week, European Union<br />
data watchdogs, fighting to protect our privacy<br />
in an age of big data, put pressure on Google<br />
over the privacy of user information.<br />
Just 48 hours later, Google potentially struck<br />
...should be for our eyes only<br />
a new blow against privacy when it posted a<br />
video preview of its new “Glass” technology --<br />
high-tech spectacles featuring a revolutionary<br />
digital interface that enable its wearers to not<br />
only view the world through Google’s eyes but<br />
also automatically photograph all that they<br />
see.<br />
“How strange is that!” CNN’s Erin Burnett<br />
exclaimed after a contemplating a “world seen<br />
through Google Glasses”.<br />
Strange indeed. But these glasses, a kind<br />
of digital surrogate for our eyes, are strange<br />
in a creepy, Hitchcockian, “Rear Window” sort<br />
of way. Or the same way that Big Brother’s<br />
ubiquitous cameras were strange in George<br />
Orwell’s “Nineteen Eighty Four.” And in the<br />
same way that a future in which “promethean”<br />
data companies like Google rule the world<br />
now appears strange.<br />
The coincidental timing of last week’s EU<br />
and Google announcements may have been<br />
unintentional, but it sure is ominous.<br />
The EU is concerned about the way in<br />
which Google has, since last March, been<br />
pooling the data of its individual users<br />
across its popular services like search, Gmail,<br />
Google+ and YouTube in order to bundle<br />
them up for <strong>ad</strong>vertisers.<br />
Its anxiety over this aggregation of our<br />
personal information is twofold. Firstly, Google<br />
has done little, if anything, to inform users of<br />
this unilateral change. Secondly, Google hasn’t<br />
offered users a way of opting out.<br />
Google insists its privacy policies respect<br />
European laws and simply help enhance user<br />
experiences. But in the eyes of the EU, those<br />
of us using products like YouTube, Gmail or<br />
Google+ are being, to borrow a Microsoft<br />
coined neologism, “Scroogled” by Google’s<br />
new privacy policy.<br />
Last October, EU watchdogs gave Google<br />
four months to revise this policy. But last week,<br />
after nothing appeared to have changed,<br />
Brussels raised its warning a bureaucratic<br />
notch, promising to take action against Google<br />
by the summer.<br />
And yet, in light of Google Glass, the EU’s<br />
concerns seem like a quaint throwback to a<br />
more innocent digital age.<br />
Watchdogs should, of course, be barking<br />
m<strong>ad</strong>ly at Google’s decision to pool our data<br />
for its <strong>ad</strong>vertising clients. Regardless of the<br />
legitimacy of such practices, I’m strongly in<br />
favor of making Google accountable, both<br />
legally and morally, for policies that so patently<br />
disregard the privacy of its users.<br />
google Class covers only part of the eye,<br />
more like an optional vision aid!<br />
But Google Glass opens an entirely new<br />
front in the digital war against privacy. These<br />
spectacles, which have been specifically<br />
designed to record everything we see,<br />
represent a developmental leap in the history<br />
of data that is comparable to moving from the<br />
bicycle to the automobile.<br />
It is the sort of r<strong>ad</strong>ical transformation that<br />
may actually end up completely destroying our<br />
individual privacy in the digital 21st century.<br />
While none of us were looking, Google<br />
-- the most data-hungry of today’s digital<br />
giants -- is reengineering mobile technology.<br />
Thanks to Silicon Valley’s m<strong>ad</strong> rush to develop<br />
wearable computing, it isn’t alone. Apple is<br />
supposedly working on its hotly-anticipated<br />
wristwatch and wearable personal data devices<br />
from companies like Nike and Fitbit are alre<strong>ad</strong>y<br />
beginning to revolutionize the healthcare<br />
industry.<br />
But there’s something particularly troubling<br />
about Google Glass. When we put on these<br />
surveillance devices, we all become spies, or<br />
scrooglers, of everything and everyone around<br />
us. By getting us to wear their all seeing digital<br />
eyeglasses, Google are metamorphosing us<br />
into human versions of those Street View vans<br />
-- now thankfully banned in Germany -- which<br />
crawl, like giant cockroaches, around our cities<br />
documenting our homes.<br />
Neither Orwell nor Hitchcock at their most<br />
terrifyingly dystopian could have dreamt up<br />
Google Glass. According to Google cofounder<br />
Sergey Brin, quoted by tech website<br />
Mashable, “Glass will also have an automatic<br />
picture-taking mode, snapping pics at a preset<br />
intervals (such as every 5 seconds).”<br />
Pics every 5 seconds! Gulp. So where<br />
will all that intimate data go? Erin Burnett’s<br />
strange “world seen through Google Glasses”<br />
is actually, as another le<strong>ad</strong>ing tech site<br />
Techcrunch notes “the world seen through<br />
Google’s omnipresent eye.”<br />
And the terabytes of data sucked up every<br />
five seconds by its omniscient glasses will,<br />
of course, flow to Google. That’s the whole<br />
business model, the very raison d’etre of<br />
Google Glass. Those pics every 5 seconds<br />
will be used to aggregate data and then to<br />
generate billions of dollars of revenue by<br />
selling <strong>ad</strong>vertising around it.<br />
One EU complaint about current Google<br />
practice, you’ll remember, was about the<br />
absence of an opt out button to enable users<br />
to say no to Google’s pooling of their data.<br />
But the problem of saying no, of opting<br />
out, becomes even more problematic with<br />
Google Glass. After all, as these Warby Parker<br />
or Ray-Ban-designed devices become more<br />
fashionable (ie: innocuous), most of us won’t<br />
even know if we are being filmed when gazed<br />
at by a bespectacled stranger.<br />
The EU watchdogs also objected to<br />
Google’s current pooling of our data in a<br />
single personalized record. And Google Glass<br />
could, I fear, become the focal point for all our<br />
data in a world where privacy no longer exists.<br />
“Everything, from Google searches to<br />
notifications to hangouts, seemingly happens<br />
in this one space,” notes Techcrunch about the<br />
spectacles. Google Glass, thus, may become<br />
the pivotal post PC, post iPod and post tablet<br />
device. A pooling of all our most intimate<br />
data, a mirror of ourselves -- the holy grail, of<br />
course, for <strong>ad</strong>vertisers.<br />
I remarked earlier that it’s hard to engineer<br />
this creepy kind of serendipity. But I may<br />
have been wrong. You see, the whole point<br />
of Google Glass is actually to successfully<br />
engineer serendipity. The creepier, the better.<br />
After all, when we wear these devices, those<br />
clever engineers at Google will know where we<br />
are all the time. So what’s to stop them serving<br />
up personalized <strong>ad</strong>vertisements for products<br />
when the gaze of our glasses rest upon those<br />
products?<br />
At the very moment we look at those new<br />
clothes in that store window, a special offer for<br />
the clothes will flash up on the digital interface<br />
of our Google Glass. How serendipitous, eh?<br />
But what to do? Is there an antidote to<br />
Google’s eyewear?<br />
Google Glass is currently in being tested<br />
with plans for a finished product to be<br />
released into the mass market next year. Last<br />
week, Google announced that a few prototype<br />
models of the spectacles would go on sale<br />
for the not exactly bargain price of $1,500.<br />
To qualify, well-heeled Google fanboys need<br />
to go to their Google+ or Twitter accounts<br />
and, in 50 words or less, using the hashtag<br />
#ifih<strong>ad</strong>glass, explain how they would use<br />
Google Glass.<br />
So, if anyone at Google happens to be<br />
re<strong>ad</strong>ing this, here’s my application:<br />
#ifih<strong>ad</strong>glass: I would make data privacy<br />
its default feature. Nobody else sees the<br />
data I see unless I explicitly say so. Not<br />
<strong>ad</strong>vertisers, nor the government, and certainly<br />
not those engineers of the human soul at<br />
the Googleplex. No, Google Glass must be<br />
opaque. For my eyes only.<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
FEATURES 35
REVIEWS<br />
PHONES<br />
Samsung <strong>Galaxy</strong> <strong>Music</strong><br />
BY JOHNSON P.<br />
INTRODUCTION:<br />
Have you ever cursed that your smartphone is not<br />
really suited to be a music player in your pocket,<br />
as you have to unlock the screen to control the<br />
player?<br />
Well, the Samsung <strong>Galaxy</strong> music is here to remedy<br />
the situation with a dedicated play/pause button<br />
plus stereo speakers, and it won’t break the bank<br />
either, as it should be with a phone targeted<br />
squarely at teens.<br />
The specs are ho-hum, but the phone promises<br />
some extras for music aficion<strong>ad</strong>os, so is it likely<br />
to win their hearts and minds the way it is?<br />
Re<strong>ad</strong> on our review to find out..<br />
DESIGN:<br />
As is customary for teen-oriented phones, we<br />
have a design with flashy color, and a lot of<br />
chrome-like rim supplied. In the case of the <strong>Galaxy</strong><br />
<strong>Music</strong>, however, we also have metal grills over<br />
the two speakers on the front - a material Samsung<br />
doesn’t use very often in its phones.<br />
The tiny handset is very easy to hold and operate with<br />
one hand, fitting comfortably in your palm with its<br />
rounded corners and tapered edges. It is on the chubby<br />
side, but nothing too grand and unbearable, while the<br />
weight is kept in check.<br />
The <strong>Galaxy</strong> <strong>Music</strong> scores points for the regular SIM card<br />
slot and the easily accessible microSD one on the left<br />
- a must if you need to hot-swap cards with your vast<br />
music collection. The memory card slot, as well as the<br />
microUSB port at the top are covered with protective<br />
flaps, that are easy to pry open or snap back into place.<br />
Looking around the sides we find a dedicated play/<br />
pause key down right, which works while the phone<br />
is locked for easily managing your music playback on<br />
the go. If you hold it, the phone goes directly into the<br />
music player, even in a locked state, so you can manage<br />
your tunes quicker.<br />
INTERFACE AND FUNCTIONALITY:<br />
The phone runs Android Ice Cream Sandwich, which<br />
is covered with Samsung’s own TouchWiz UI on top.<br />
It offers no surprises, with the typical Samsung set of<br />
widgets, and an abundance of connectivity toggles in<br />
the notification bar.<br />
There is a pretty spare use of transparencies and<br />
transitional animations compared to the large caliber<br />
Galaxies, as the processor is not very powerful to<br />
support<br />
those<br />
freely.<br />
Apart<br />
from<br />
its own<br />
apps and<br />
media Hubs,<br />
Samsung has<br />
only prelo<strong>ad</strong>ed<br />
Quickoffice for<br />
opening MS Office and<br />
PDF files.<br />
As you can easily guess, typing on the smallish display<br />
is not very easy, especially with bigger hands, and the<br />
fact that the keyboard doesn’t turn in landscape mode<br />
isn’t helping either.<br />
PROCESSOR AND MEMORY:<br />
The 850 MHz processor is single-core, but with a<br />
Cortex-A9 architecture, so it has enough power to pull<br />
through your daily tasks and interface navigation, but<br />
often has hiccups while lo<strong>ad</strong>ing apps, or running more<br />
demanding ones.<br />
The <strong>Galaxy</strong> <strong>Music</strong> has 512 MB of RAM, and 4 GB of<br />
internal memory, of which 1.7 GB are user-available, but<br />
it also offers a microSD card slot on the left for storage<br />
expansion with up to 32 GB cards.<br />
INTERNET AND CONNECTIVITY:<br />
The browser on the <strong>Galaxy</strong> <strong>Music</strong> is a basic ICS version,<br />
with no Adobe Flash support, and somewhat choppy<br />
panning and scrolling thanks to the comparatively slow<br />
processor. The low pixel density is a bummer, too, but<br />
you are unlikely to use it on such a tiny screen for hours<br />
36 pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
36<br />
on end anyway.<br />
The handset sports the basic connectivity<br />
options - 7.2 Mbps HSDPA downlo<strong>ad</strong>s, Wi-Fi,<br />
Bluetooth, GPS and FM R<strong>ad</strong>io.<br />
CAMERA:<br />
The 3 MP camera on the back of the phone<br />
doesn’t have a flash, and the interface is pretty<br />
basic, hinting at the limited functionality of<br />
the unit. Still, you get a few shooting modes,<br />
including Panorama, and a few scene presets,<br />
as well as some standard color effects.<br />
Going into the Camera app is pretty quick<br />
directly from the lock screen, and focusing and<br />
taking a shot is very fast, too, with minimal<br />
shutter lag.<br />
MULTIMEDIA:<br />
Despite its <strong>Music</strong> designation, the phone<br />
generAl FeAtureS<br />
In Sales Package Handset, charger, Battery (<strong>13</strong>00 mAh), Data cable,<br />
He<strong>ad</strong>set, user Manual<br />
Form Bar<br />
SIM Dual SiM, gSM + gSM<br />
Touch Screen yes, capacitive<br />
Business Features Pushmail<br />
Call Features conference call, loudspeaker<br />
Handset Color ceramic White<br />
PLATFORM<br />
Operating Freq gSM - 850, 900, 1800, 1900; uMtS - 2100<br />
OS Android v4 (ice cream Sandwich)<br />
User Interface touchWiz uX<br />
Java yes<br />
Processor 850 MHz cortex-A9<br />
DISPLAY<br />
Type lcD<br />
Size 3 inches<br />
Resolution QVgA, 240 x 320 Pixels<br />
Color 262 K<br />
CAMERA<br />
Primary Camera yes, 3 Megapixel<br />
Video Recording yes, 25 fps<br />
zoom Digital zoom - 2x<br />
Other Camera Features<br />
DIMENSIONS<br />
Size 59x110x12.25 mm<br />
Weight 107 g<br />
BATTERY<br />
Type li-ion, <strong>13</strong>00 mAh<br />
Talk Time 15 hrs (2g)<br />
Standby Time 500 hrs (2g)<br />
MEMORY AND STORAgE<br />
Internal 4 gB<br />
Expandable Memory microSD, upto 32 gB<br />
geo-tagging, touch Focus, Full Focus, Auto Focus,<br />
Photo effects, White Balance, cMOS Sensor, Photo<br />
Quality, image editor<br />
doesn’t offer anything extra in the alre<strong>ad</strong>y<br />
pretty rich TouchWiz tunes player. The usual<br />
song categorization options are present, along<br />
with the <strong>Music</strong> Square mood matrix. The<br />
player interface is easy to operate, with sound<br />
effects and equalizers directly accessible while<br />
the song is playing with the tap of a button.<br />
There are two stereo speakers, top and<br />
bottom at the front, and the supplied Sound<br />
Alive and SRS Surround Sound modes do<br />
make the music more intense, yet overall the<br />
speakers are nothing to write home about,<br />
not so much in terms of strength, which is fine,<br />
but in terms of sound quality, which is about<br />
average, re<strong>ad</strong> nothing impressive when it<br />
comes to clarity and fullness.<br />
CONCLUSION:<br />
Depending on the way it is priced, the<br />
FULL SPECIFICATIONS<br />
Memory 512 MB rAM<br />
INTERNET & CONNECTIVITY<br />
Internet Features email<br />
Preinstalled Browser Android<br />
gPRS, EDgE yes<br />
3g yes, 7.2 Mbps HSDPA; 5.76 Mbps HSuPA<br />
Wifi yes, 802.11 b/g/n<br />
USB Connectivity yes, micro uSB, v2<br />
Tethering Wi-fi Hotspot<br />
Navigation Technology<br />
A-gPS, glOnASS, with google Maps<br />
Bluetooth yes, v3, Supported Profiles (HS, A2DP, AVrcP)<br />
Audio Jack 3.5 mm<br />
DLNA yes<br />
MULTIMEDIA<br />
<strong>Music</strong> Player yes, Supports WAV, FlAc, MiDi, MP3, eAAc+<br />
Video Player yes, Supports PVX, 3gP, AAc, VP8, AAc+, MP4,<br />
H.263, H.264, MKV, MPeg4, AAc+V2, AMr, AMrnB<br />
FM yes<br />
Sound Enhancement SrS Surround Sound, SoundAlive Solution<br />
Ringtone MP3, 64 Polyphonic<br />
OTHER FEATURES<br />
SAR Value 0.754 W/Kg<br />
Call Memory yes<br />
SMS Memory yes<br />
Phone Book Memory yes<br />
Sensors Accelerometer, Proximity Sensor, compass<br />
Additional Features Kies Pc Application, Mini SiM, Wi-Fi Direct, Video<br />
Streaming, calendar, clock, Alarm, DrM Supported<br />
(OMA 1.0), Voice input<br />
Important Apps google Mobile Services, Samsung Apps, <strong>Music</strong><br />
Hub, game Hub lite, google talk, google+,<br />
chatOn, Play Store<br />
WARRANTY<br />
1 year manufacturer warranty for Phone and 6 months warranty for in the box<br />
accessories<br />
Price: Approx. ugX 550,000<br />
Samsung <strong>Galaxy</strong> <strong>Music</strong> could turn out one<br />
unpretentious hottie amongst teens, as it has<br />
the prerequisite colored looks, with chromelike<br />
blingery and extra music features thrown<br />
in. The dedicated play/pause/music player<br />
access key on the side is the only thing that<br />
makes it stand out as a music player, though,<br />
since the two stereo speakers are of pretty<br />
average quality.<br />
There are no major gripes with the handset<br />
but the smallish screen and the low pixel<br />
density, as well as the lack of some sensors.<br />
The <strong>Galaxy</strong> <strong>Music</strong> sports a a hot-swappable<br />
microSD slot and a regular SIM card one,<br />
which are a plus now<strong>ad</strong>ays, and it also offers<br />
a pretty good call quality, making it a versatile<br />
affordable device for music aficion<strong>ad</strong>os.<br />
REVIEWS 37
REVIEWS 38<br />
LAPTOPS & DESKTOPS<br />
NOKIA Lumia 920<br />
NOKIA UNVEILED THE LUMIA 920 and Lumia<br />
820 way back in September last year and,<br />
expectedly, it took quite a while for the phones<br />
to find their way on to East Africa. This month,<br />
though, MTN Uganda launched the phone in<br />
Uganda, and here’s our slightly belated review<br />
of the Nokia Lumia 920.<br />
HARDWARE/ DESIGN<br />
The first thing you notice about the Nokia<br />
Lumia 920, no doubt, is the bulk. The device<br />
may not be as large as the <strong>Galaxy</strong> Note II,<br />
but somehow Nokia has managed to make it<br />
heavier than Samsung’s phablet. Once you get<br />
past the weight, however, there’s plenty to like.<br />
The Nokia Lumia 920 is solidly built out<br />
of a polycarbonate unibody shell that goes<br />
all around the device and offers a welcome<br />
change if you’ve been living in the Samsung<br />
world of plastic for too long. The left side<br />
of the phone is completely bare, giving<br />
way to the Micro-SIM slot on the top left.<br />
The 3.5mm he<strong>ad</strong>phone/mic jack is at the<br />
centre of the top edge, <strong>ad</strong>jacent to a noisecancelling<br />
microphone. The right edge has the<br />
volume rocker, power-button and the camera<br />
button, in a typical Windows Phone button<br />
arrangement.<br />
The bottom edge comes with the micro-<br />
USB port flanked on either side by a rather<br />
cute looking speaker grill. Nokia Lumia 920 is<br />
one of the few phones that manages to have<br />
two visible screws without flipping the ugly<br />
switch over. The back has Nokia/ Carl Zeiss<br />
branding alongside the dual-LED flash. The<br />
front has an earpiece grill and a front camera<br />
next to Nokia branding at the top, with three<br />
capacitive touch buttons rounding off a typical<br />
Windows Phone device look.<br />
DISPLAY<br />
Nokia has put in plenty of work on the display<br />
of the Lumia 920 and thrown in a helping of<br />
buzzwords for good measure – PureMotion<br />
HD+, ClearBlack and the likes. So does that<br />
translate into a great viewing experience? By<br />
and large, yes.<br />
Nokia has ditched the AMOLED display<br />
found in the Lumia 900 and gone with a 4.5inch<br />
IPS LCD with 768×1280 resolution in its<br />
latest flagship. We’ve always been fans of truer<br />
colours that the IPS LCD represent and while<br />
colours on AMOLED may look ‘prettier’, even<br />
its biggest proponents have started moving<br />
away from the technology, given the obvious<br />
inaccuracies in colour reproduction.<br />
Overall, the Nokia Lumia 920 offers best in<br />
class viewing experience, indoors as well as<br />
outdoors. Yes, we did give the touchscreen<br />
a spin while wearing gloves and yes, it does<br />
work as <strong>ad</strong>vertised.<br />
CAMERA<br />
Much has been written about the camera in<br />
the Nokia Lumia 920. The camera carries the<br />
PureView moniker, m<strong>ad</strong>e famous by the 41megapixel<br />
Nokia 808. Unfortunately, the Nokia<br />
Lumia 920 does not have the 41-megapixel<br />
sensor or the oversampling technology found<br />
in the 808, so we’re not sure what component<br />
of ‘PureView’ technology has been carried<br />
forward here. Nonetheless, the camera doesn’t<br />
let us down.<br />
There are two things that the Nokia<br />
Lumia 920 camera does better than any<br />
other camera-phone out there. The first is<br />
photography under low-light conditions,<br />
where the Lumia 920′s imaging capabilities<br />
really come to light (excuse the b<strong>ad</strong> pun).<br />
Images clicked in poor light conditions using<br />
the Lumia 920 are much better than those<br />
clicked with the iPhone 5, perhaps the Lumia<br />
920′s closest match in low-light photography.<br />
However, if you really cherish a shot, we<br />
would recommend clicking an extra snap<br />
or two, since the results can be a little bit<br />
unpredictable in terms of which object gains<br />
focus.<br />
The other area where we can safely say<br />
the Lumia 920 is lightyears ahe<strong>ad</strong> of the<br />
competition if image stabilisation. We shot<br />
side-by-side videos taken with the Lumia<br />
920 and competition, and the difference was<br />
like night and day. Nokia has suspended the<br />
entire Lumia 920 optical assembly using tiny<br />
springs that absorb shocks and the results are<br />
stunning. If you are fond of taking videos on<br />
the move, or just have the hands of a drunken<br />
sailor like us, you’ll love the Nokia Lumia 920′s<br />
cameras.<br />
Windows Phone 8 introduced the concept<br />
of camera lenses, which let you see and click<br />
images in a “different light”. Nokia Lumia<br />
920 comes with Bing Vision, Panorama,<br />
Cinemagraph and Smart Shoot lenses to cater<br />
to various shooting moods and requirements.<br />
SOFTWARE/ UI<br />
The Nokia Lumia 920 comes with Windows<br />
Phone 8, Microsoft’s latest mobile-OS<br />
that ships with multiple improvements like<br />
enhanced performance, multi-core processor<br />
support, NFC and more. Lumia 920, of course,<br />
benefits from these and the focus in this review<br />
will be to highlight the non-core software<br />
components of the Lumia 920.<br />
While Windows Phone 8 doesn’t offer<br />
much flexibility to the manufacturer in terms<br />
of customising the OS, Nokia has managed<br />
to include a few apps that may well prove<br />
to be the differentiator compared to the<br />
competition. The Lumia 920 comes with<br />
popular apps like Nokia Drive, Nokia Maps<br />
and Nokia <strong>Music</strong>, as well as other Nokia apps<br />
like Nokia Care and Nokia City Lens. We’re big<br />
fans of the Nokia Drive app – as documented<br />
in the Nokia 808 review and as far as we<br />
are concerned, Nokia continues to set the<br />
benchmark in navigation apps, even ahe<strong>ad</strong> of<br />
Google Maps.<br />
Two other services we like are Nokia Maps,<br />
which is a huge improvement over the stock<br />
Bing Maps and Nokia <strong>Music</strong>, that offers<br />
unlimited music free for a year. We’ve h<strong>ad</strong><br />
mixed results with the City Lens app, though<br />
your mileage may vary. All in all, thanks to a<br />
small but important lineup of exclusive apps,<br />
the Lumia 920 offers a compelling option once<br />
you’ve decided to go ahe<strong>ad</strong> with Windows<br />
Phone 8.<br />
But is Windows Phone 8 itself worth your<br />
time? Sure, if you can look past a rather bare<br />
looking app store and other annoyances like<br />
the app-installation procedure that requires a<br />
few too-many clicks to get back to what we<br />
are doing. Windows Phone could surely do<br />
with an improved notification system as well.<br />
But if you’re a first-time smartphone buyer,<br />
or looking for a change from the monotony<br />
of the Android/ iOS world, Windows Phone 8<br />
Compared to Samsung’s galaxy SIII as well as most other existing high-end smartphones, the<br />
Lumia 920 is definitely bulky - with a larger screen area.<br />
offers a pretty solid alternative.<br />
PERFORMANCE/ BATTERY LIFE<br />
Windows Phone 8 paved the way for multicore<br />
processors to find their way to Microsoft’s<br />
mobile world, with earlier versions limited to<br />
single-core processors. The current generation<br />
of flagships including the Lumia 920 promptly<br />
utilise the enhanced capabilities by shipping<br />
with dual-core chips, and the benefit, is there<br />
to be seen.<br />
The Nokia Lumia 920 suffered from no<br />
noticeable delays during our time spent<br />
with the device and handled pretty much<br />
everything we threw at it without any<br />
problems. Battery life is unlikely to be a<br />
problem even for heavy users, and you can<br />
expect to go by an entire day on a single<br />
recharge.<br />
pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
VERDICT<br />
Nokia Lumia 920′s release can perhaps be<br />
termed unfortunately timed. The current<br />
generation of flagship Android devices from<br />
the likes of Samsung and HTC have been<br />
around for a while and have benefited from<br />
one or more rounds of price-cuts, to the point<br />
that they are available at a considerable price<br />
<strong>ad</strong>vantage compared to the Lumia, even when<br />
their original prices weren’t too dissimilar<br />
compared to the 920′s. In this environment,<br />
it is understandable that customers would be<br />
tempted to pick up more impressively specced<br />
devices at lower prices.<br />
Having said that, both the camera and the<br />
display are as good as money can buy at the<br />
moment and if you’re willing to give Windows<br />
Phone a spin, we definitely recommend<br />
giving the Lumia 920 a second look. At UGX<br />
2,2500,000/= (MTN Uganda) the Lumia 920 is<br />
by far the most expensive Windows 8 phone<br />
on the market.<br />
However, given Lumia 920′s superiority over<br />
the 8X in terms of the camera, display as well<br />
as bundled apps, we give Nokia’s offering a<br />
slight edge.<br />
Re<strong>ad</strong> more reviews at:<br />
http://reviews.pctechmag.com<br />
Are you a good reviewer? We’re hiring!<br />
Email: editor@pctechmagazine.com or simply<br />
tweet @pctechmagazine.<br />
REVIEWS 39
GALLERY<br />
APPS<br />
Review: Orange Money TOSHIBA Satellite P845t-101<br />
By BrigHt OnAPitO<br />
So NoW IT IS oFFIcIAl, oRANGe Uganda<br />
limited has joined the informal banking sector<br />
by introducing their version of mobile money<br />
dubbed orange money. This brings the number<br />
of mobile money operators to 5 after Airtel,<br />
mTN, UTl and Warid launched their platforms<br />
earlier on.<br />
THE 2011/2012 Uganda Communications<br />
Commission half year posts and market<br />
review puts the number of mobile<br />
subscribers at 16.6 million, which is nearly half<br />
the number of Uganda’s population. MTN<br />
alone has about 3.5 million registered mobile<br />
money subscribers and as the de<strong>ad</strong>line for<br />
registering mobile subscribers fast approaches,<br />
the Mobile Network Operators are scrambling<br />
to have all their clients registered.<br />
Mobile money has been such a huge<br />
phenomenon in Uganda. A 2011 Gallup,<br />
Inc report estimates that 43% of all money<br />
transfers carried out was by mobile money.<br />
That is huge! The numbers are surely going<br />
up, more so that a new player has joined the<br />
market. Mobile money as we know it has h<strong>ad</strong><br />
its glitches. As far as scalability and reliability<br />
are concerned, mobile money users have<br />
suffered the pains of incomplete transactions,<br />
network time-outs and blackouts. That<br />
moment when you are stranded in town and<br />
need quick cash only to be told by the mobile<br />
money agent that ‘the network is down’!<br />
Such has been the plight of mobile money<br />
subscribers in Uganda. So the big question is:<br />
Do we need another mobile money operator<br />
in this market? What innovations does Orange<br />
money bring to this alre<strong>ad</strong>y chaotic spectrum?<br />
I took time to register for Orange Money so<br />
as to see what makes it tick or screech and this<br />
is what I found out:<br />
FRONTEND<br />
I don’t see anything new here. Orange Money<br />
uses the tr<strong>ad</strong>itional architecture consisting of<br />
Unstructured Supplementary Service Data<br />
(USSD), Short Message Service (SMS) and<br />
USSD/SMS servers and web services, which<br />
is similar to all the other mobile money<br />
operators. Now while USSD(see the screenshot<br />
below) is compatible with just about any GSM<br />
mobile phone, in this day and age of mobile<br />
Apps, it simply lacks in terms of user interface<br />
and experience. We thought that perhaps it’s<br />
was high time the Telecoms drummed up to<br />
the beat of intuitive native mobile Apps that<br />
offer better user experience and are much<br />
intuitive for smartphone users while keeping<br />
USSD for the feature phones. But alas, it’s the<br />
same old.<br />
REGISTERING<br />
It was so easy for me to register for Orange<br />
money. It actually took me less than 10<br />
minutes. No need for passport photos<br />
because they have those smart phones for<br />
image capture. Once my details were in their<br />
systems my Orange Money account was<br />
activated almost instantly. I thought this was<br />
great!<br />
NETWORk RELIABILITY<br />
Orange Money alre<strong>ad</strong>y has a he<strong>ad</strong> start for<br />
a fact that the Orange network is not overly<br />
congested like its competitors and is still<br />
regarded as the most efficient mobile network<br />
(according to the Uganda Communications<br />
Commission). So far the application currently<br />
runs flawlessly on my Samsung <strong>Galaxy</strong>. Only<br />
time will tell how reliable the service will be<br />
as the number of users increase. I will be<br />
watching closely.<br />
SECURITY FEATURES<br />
Orange Money has what they call the Multiple<br />
Transaction Rule, which protects users<br />
from making the same transaction twice. A<br />
message is sent to the sender asking them to<br />
confirm if they wish to repeat that transaction.<br />
Also, when they send money for the first<br />
time the recipient will be sent an SMS asking<br />
them to confirm the transaction by entering<br />
the sender’s number. Considering that they<br />
(most likely) won’t know the sender’s phone<br />
number, the system automatically sends back<br />
the money and transaction fees after 5 days<br />
if there is no confirmation. This is a smart<br />
innovation they have introduced that the other<br />
operators lack.<br />
COST OF TRANSACTIONS<br />
Comparatively, there is no significant<br />
difference in transaction cost, though overall<br />
Orange Money charges are slightly higher<br />
than the other competitors. Also, the<br />
maximum transaction limit is much lower that<br />
the competition. You can transact a mere<br />
maximum of UGX 2,000,000 while you can do<br />
up to UGX 10,000,000 with UTL. I get a feeling<br />
this is a strategy to keep the network traffic<br />
under check.<br />
UTILITY PAYMENTS<br />
The only things I can buy using Orange Money<br />
are airtime and data bundles. Hopefully they<br />
will integrate other utility service payments in<br />
the short run.<br />
Some features that I think Orange Money<br />
(and all the other network providers) need<br />
to include in their applications among others<br />
include session caching. Sometimes the<br />
network might time out when the transaction<br />
is almost complete and the user has to start<br />
the process again. That can be very frustrating<br />
for the users. How about the user being able<br />
to continue right where they stopped?<br />
The developers ask — do they have an API?<br />
The software engineer that I am is also looking<br />
for ways to integrate third party services to<br />
any application. There is still a major lack of<br />
Application Programming Interfaces (APIs) to<br />
accomplish this. The fancy name aside, an API,<br />
just enables you to do more. If Orange Money<br />
could <strong>ad</strong>dress this need they could experience<br />
a huge demand for their service considering<br />
that software developers will le<strong>ad</strong> the way.<br />
This will be a deal breaker. Mobile technology<br />
is <strong>ad</strong>vancing exponentially and the mobile<br />
operator willing to embrace these changes will<br />
be ahe<strong>ad</strong> of the game. One of these <strong>ad</strong>vances<br />
is Near Fields Communication (NFC) which I<br />
believe is going to revolutionalize how mobile<br />
transactions are carried out in the near future.<br />
CONCLUSION<br />
Other than the promise of a more reliable<br />
and secure mobile money service, Orange<br />
money brings absolutely nothing new to<br />
the mobile money industry and we found<br />
no differentiating killer feature just yet. The<br />
platform is still “closed” and tightly controlled<br />
by the carrier just like all other platforms giving<br />
no chance for third party providers like say<br />
payment aggregators to use or extent the<br />
benefits of the system.<br />
—The author is a contributor for The<br />
TechPost (www.techpost.ug)<br />
TOSHIBA’S SATELLITE P845T-101 takes<br />
everything we loved about the Asus VivoBook<br />
S200 and <strong>ad</strong>ds an extra helping of raw<br />
processing power. Its third-generation Intel<br />
Core i5-3317U processor runs at 1.7GHz, but<br />
its Turbo Boost technology can increase the<br />
clock speed to 2.6GHz when it’s within certain<br />
thermal limits.<br />
This makes it plenty fast enough for<br />
everyday applications, as well as more<br />
demanding programs that benefit from<br />
multiple cores.<br />
The Core i5’s built-in Intel HD Graphics<br />
4000 GPU provides the visuals, but this<br />
laptop performed better than most in our<br />
Dirt Showdown benchmark, scoring 19fps at<br />
720p with graphics options set to High and<br />
4x anti-aliasing enabled. This is a much<br />
better score than we’ve seen on other<br />
laptops with similar integrated chips,<br />
and we only h<strong>ad</strong> to lower the settings<br />
to Medium to achieve a more playable<br />
30fps.<br />
The real highlight of the P845t-101 is its<br />
14in 10-point touchscreen. It’s very responsive<br />
and a joy to use whether you’re browsing the<br />
web, scrolling through the Windows Store<br />
or zooming in and out of Google Maps. The<br />
only slight worry we h<strong>ad</strong> was with how much<br />
it wobbled when we tapped icons or the<br />
onscreen keyboard, but it has just enough<br />
weight to stop it rocking on the table if you jab<br />
the screen particularly hard.<br />
The downside to having a touchscreen is<br />
that you have to deal with fingerprints, but<br />
thanks to its glossy finish they weren’t very<br />
noticeable unless the screen was switched off<br />
or particularly dark. In fact, we h<strong>ad</strong> more issues<br />
with reflections than fingerprints in general<br />
use. One <strong>ad</strong>vantage of a glossy display is<br />
bright, vivid colours, and the screen certainly<br />
m<strong>ad</strong>e our solid-colour test images extremely<br />
vibrant.<br />
The full-size Chiclet-style keyboard is<br />
comfortable to type on. The well-spaced keys<br />
provide plenty of bounce and tactile feedback,<br />
and a white LED backlight illuminates the<br />
keyboard in low light. We didn’t like the way<br />
the keyboard picked up fingerprints, though.<br />
It’s a small complaint, but we could easily see<br />
where we’d been typing, even after a short<br />
period, and the prints weren’t particularly easy<br />
to clean off.<br />
The smooth all-in-one touchp<strong>ad</strong> didn’t<br />
pick up fingerprints and didn’t<br />
get in the way while typing,<br />
even though it’s not quite in<br />
the centre of the wrist rest.<br />
Multi-touch gestures such<br />
as pinching to zoom were<br />
accurate, and we could easily<br />
use it to bring up Windows<br />
8’s Charms Bar and switch<br />
between windows. Clicking<br />
icons and folder links<br />
sometimes sent our cursor<br />
jolting upwards, as the<br />
buttons are incorporated<br />
into the rest of the<br />
touchp<strong>ad</strong>,<br />
but overall<br />
it wasn’t too much<br />
of a nuisance.<br />
If you find yourself away from<br />
the mains, the P845t should just about last<br />
you most of a working day, as it lasted five<br />
hours and 56 minutes in our light-use battery<br />
life test. It also has a wide range of ports,<br />
including three USB3 ports, a multiformat SD<br />
card re<strong>ad</strong>er, a he<strong>ad</strong>phone and microphone<br />
jack, a DVD rewriter, an Ethernet port and<br />
an HDMI and VGA input for connecting an<br />
external display. The range of video outputs<br />
is useful, as you’ll be able to use practically<br />
any external display from an HD TV to an old<br />
projector.<br />
Our only concern is the price. At £650, it’s<br />
in direct competition with the Toshiba Satellite<br />
L855-148, which is both much faster and<br />
more powerful than the P845t. The Satellite<br />
L855-148 doesn’t have a touchscreen, but it’s<br />
a much better buy.<br />
This makes the P845t hard to recommend<br />
outright, but for those who need a<br />
touchscreen, the P845t is perfectly in the<br />
middle ground between the budget price and<br />
power of the Asus VivoBook S200 and the<br />
vastly more expensive Ultrabooks such as the<br />
Dell XPS 12 and Asus Taichi. If you don’t need<br />
a touchscreen laptop, we recommend the<br />
Toshiba Satellite L855-148.<br />
40<br />
40 pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
SUMMARY<br />
PROCESSOR: 1.7GHz Intel Core i5-3317U<br />
RAM: 6GB<br />
STORAGE: 640GB hard disk<br />
GRAPHICS: Intel HD Graphics 4000<br />
OPTICAL: DRIVE DVD+/-RW +/-DL, DVD-<br />
RAM<br />
DISPLAY: 14in widescreen LCD (1,366x768)<br />
OPERATING SYSTEM: Windows 8<br />
DIMENSIONS: 24x349x234mm, 2kg<br />
POWER CONSUMPTION: 1W standby, 12W<br />
idle, 33W active<br />
WARRANTY: One-year RTB<br />
PART CODE: PSPJ5E-00C00JEN<br />
DeSIGN<br />
FeATUReS<br />
peRFORMANCe<br />
Reviewed by Expert Reviews<br />
Professional Web Development?<br />
www.<strong>ad</strong>noteplus.com / info@<strong>ad</strong>noteplus.com<br />
41<br />
GALLERY
GALLERY<br />
42<br />
42 pc tech ISSUE 25 FEBRUARY 20<strong>13</strong><br />
ISSUE 25 FEBRUARY 20<strong>13</strong> pc tech<br />
43<br />
GALLERY
VISION<br />
SPECIFICATION STATUS<br />
First Published FEBRUARY 2010<br />
Issues Published 25<br />
Circulation UGANDA, RWANDA, KENYA, GHANA, NIGERIA, South Africa<br />
Frequency MONTHLY<br />
Pages 52<br />
Price (Local) UGX 5000, KSH. 200, FRW 1200, USD 5, GHS 8<br />
Quality GLOSSY<br />
Milestones September 22, 2010: Launched in Ghana, December 2010: PC Tech won<br />
the Young Achievers Award ICT Category (2011). PC Tech Named in Top<br />
10 most popular websites in Uganda (Alexa.com)<br />
Other Initiatives PC Tech “Educate”, CTBuS (The Ac<strong>ad</strong>emuc Journal of PC Tech), Digital<br />
Learning Africa (Online Resource Platform), PC Tech Directory, PC Tech<br />
Jobs, Africa Internet & Mobile Entrepreneurs’ Conference and AdNote+<br />
VERDICT You decide.<br />
To be the le<strong>ad</strong>ing media organization that<br />
promotes openness and collaboration on<br />
sustainable innovations in Technology, Business<br />
and Society<br />
MISSION<br />
To create and disseminate inprint and online<br />
products on Technology, Business & Society that<br />
have a global perspective but contextually relevant<br />
to Africa<br />
FACT FILE<br />
FEATURED COVERS<br />
www.pctechmagazine.com<br />
Africa’s Most Contemporary Technology Magazine<br />
Plot 14 Martyrs Lane, Ntinda, Kampala. Website: www.<strong>ad</strong>noteplus.com Twitter: @<strong>ad</strong>noteplus Facebook: /<strong>ad</strong>noteplus Phone: (+256) 792 619812/0782924374 Email: info@<strong>ad</strong>noteplus.com