CLOSING KEYNOTE
D2T2%20-%20Peter%20blasty%20Geissler%20-%20Breaking%20Naive%20ESSID%20WPA2%20Key%20Generation%20Algorithms D2T2%20-%20Peter%20blasty%20Geissler%20-%20Breaking%20Naive%20ESSID%20WPA2%20Key%20Generation%20Algorithms
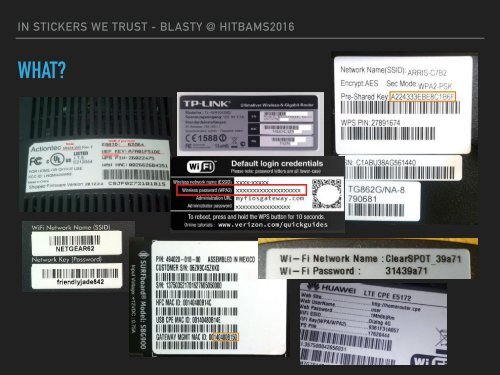
IN STICKERS WE TRUST - BLASTY @ HITBAMS2016 WHAT? ▸ Default WIFI credentials. Yep, in 2016. ▸ Recovering “secret” algorithms ▸ Dealing with painful/alien code
IN STICKERS WE TRUST - BLASTY @ HITBAMS2016 WHAT?
- Page 1 and 2: CLOSING KEYNOTE THE ERA OF CYBER WA
- Page 3 and 4: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 5: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 9 and 10: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 11 and 12: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 13 and 14: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 15 and 16: TEXT SOIC CLIPS
- Page 17 and 18: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 19 and 20: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 21 and 22: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 23 and 24: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 25 and 26: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 27 and 28: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 29 and 30: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 31 and 32: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 33 and 34: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 35 and 36: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 37 and 38: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 39 and 40: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 41 and 42: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 43 and 44: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 45 and 46: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 47 and 48: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 49 and 50: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 51 and 52: IN STICKERS WE TRUST - BLASTY @ HIT
- Page 53: IN STICKERS WE TRUST - BLASTY @ HIT
IN STICKERS WE TRUST - BLASTY @ HITBAMS2016<br />
WHAT?